Poiana – Reverse shell over TOR network using hidden services
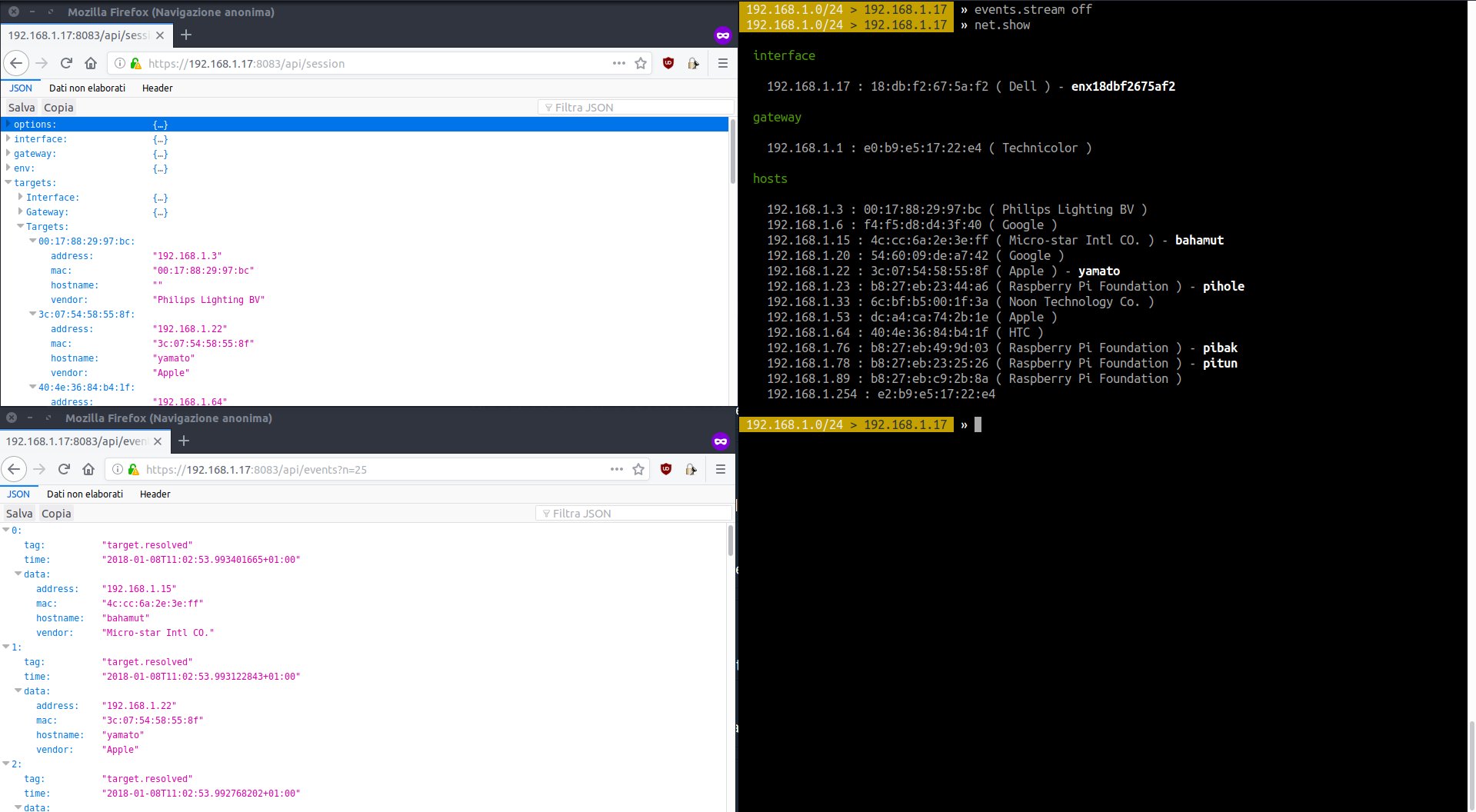
Reverse shell over TOR network using hidden services Reverse shell over TOR network using hidden services using this tool will allow you to spawn a reverse Metasploit shell over the TOR network. Using Tor2Web, the victim doesn’t need to have tor or ncat. So, using Tor2Web our victim can establish a connection to our hidden … Read more