Gallia – Extendable Pentesting Framework
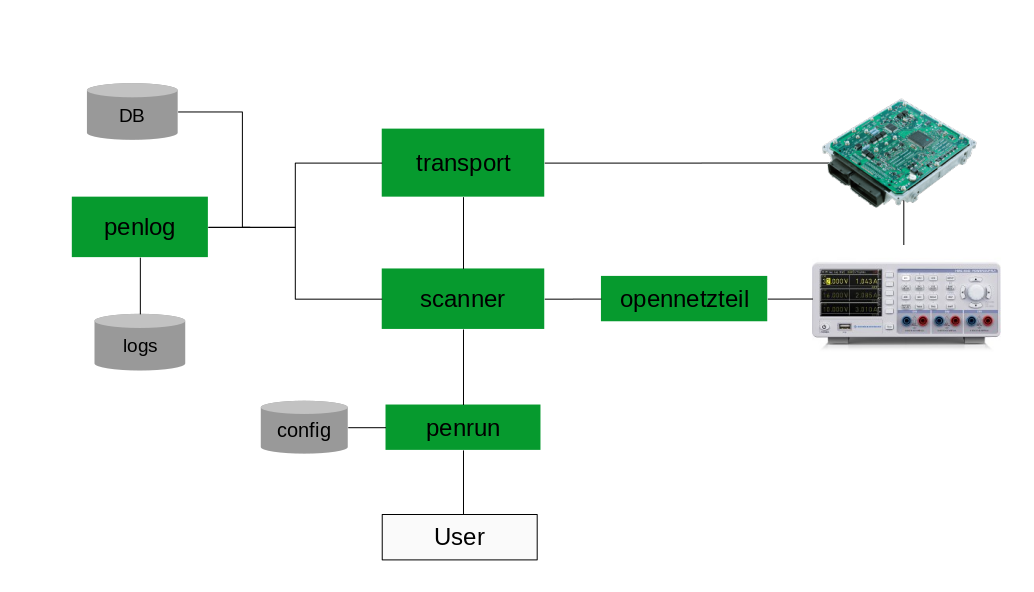
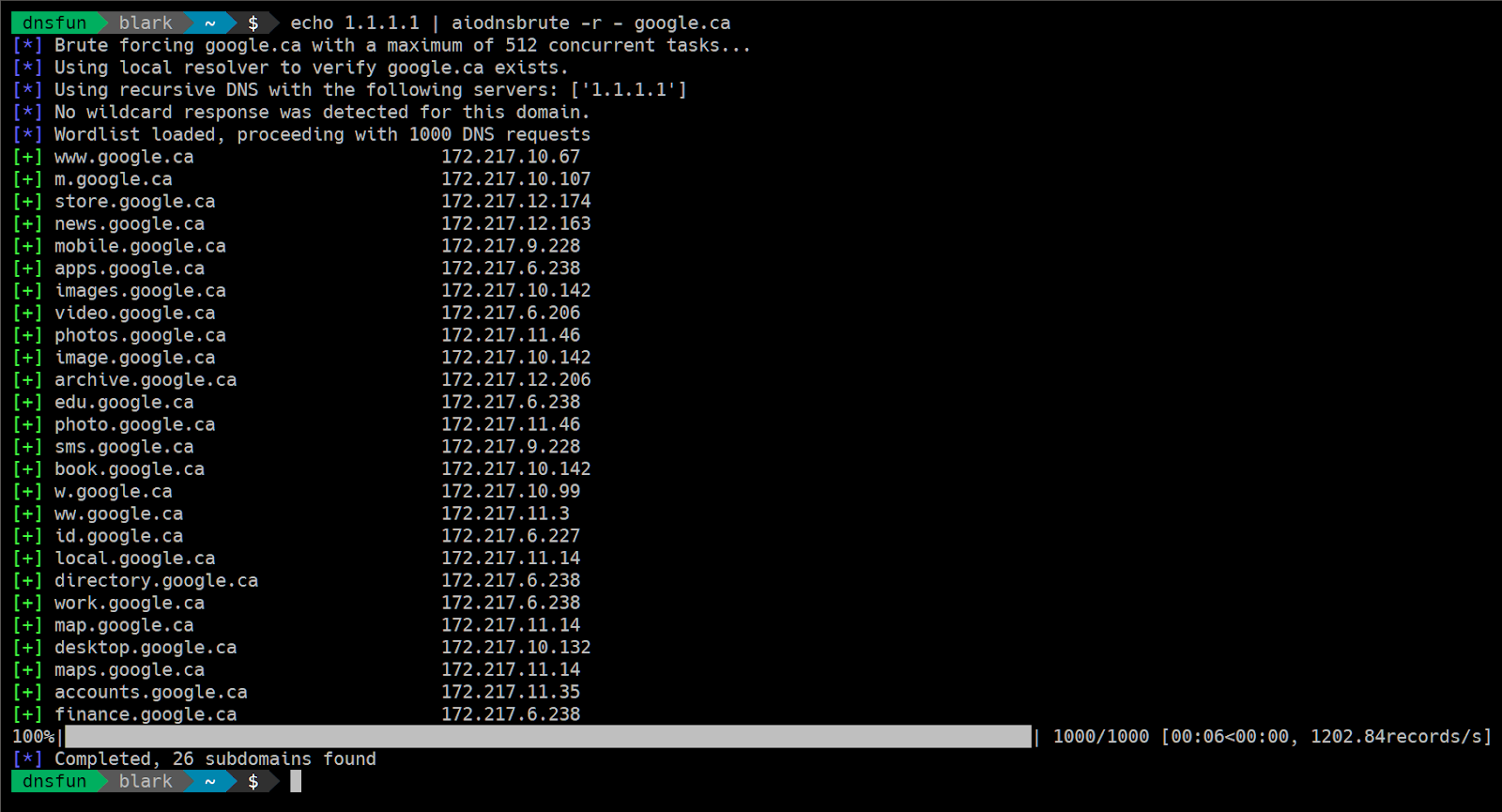
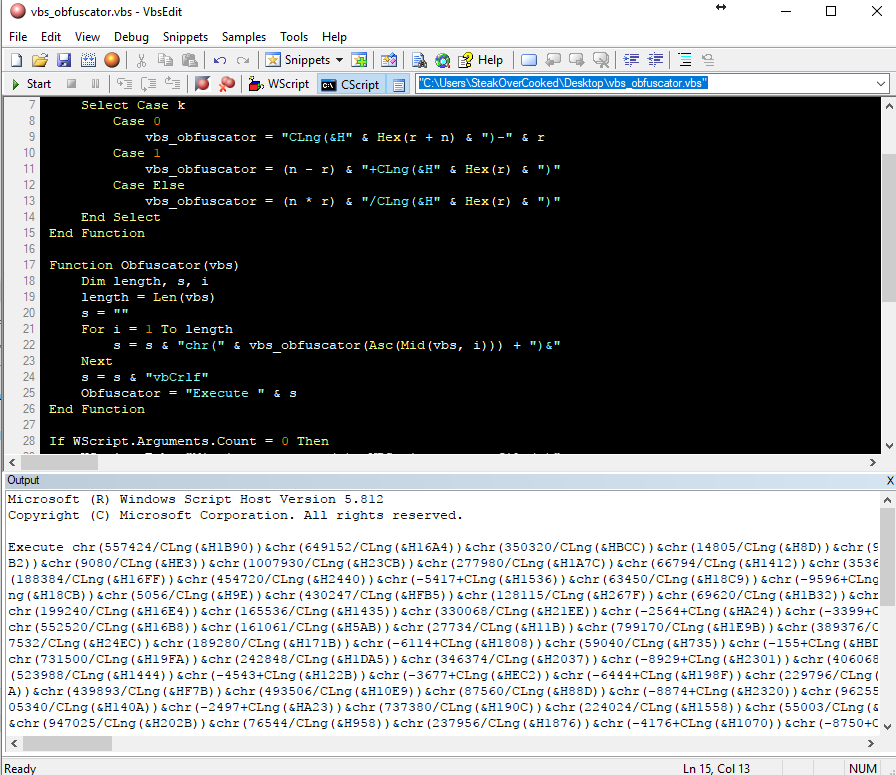
Gallia is an extendable pentesting framework with a focus on the automotive domain. The scope of Gallia is conducting penetration tests from a single ECU up to whole cars, with the main focus on the UDS interface. Taking advantage of this modular design, the logging and archiving functionality was developed separately. Acting as a generic … Read more