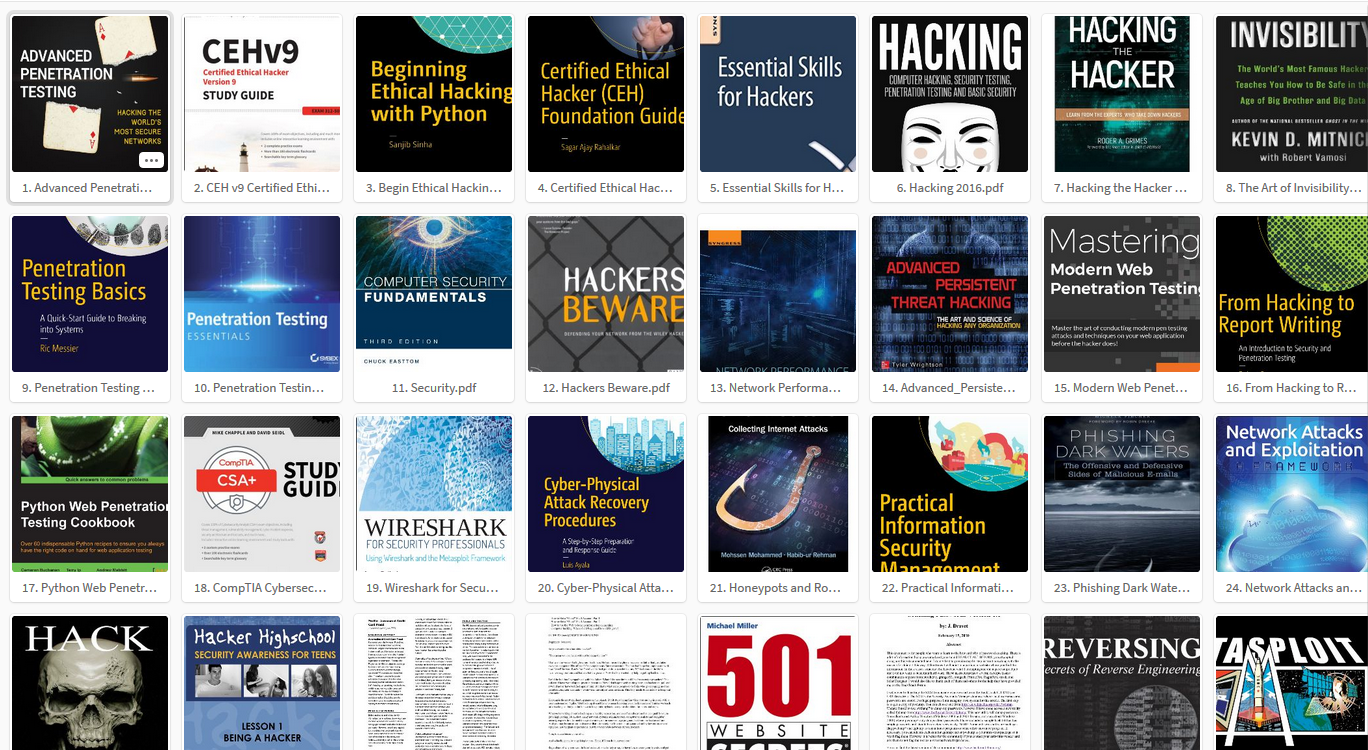
Penetration Testing with the Bash shell PDF eBook
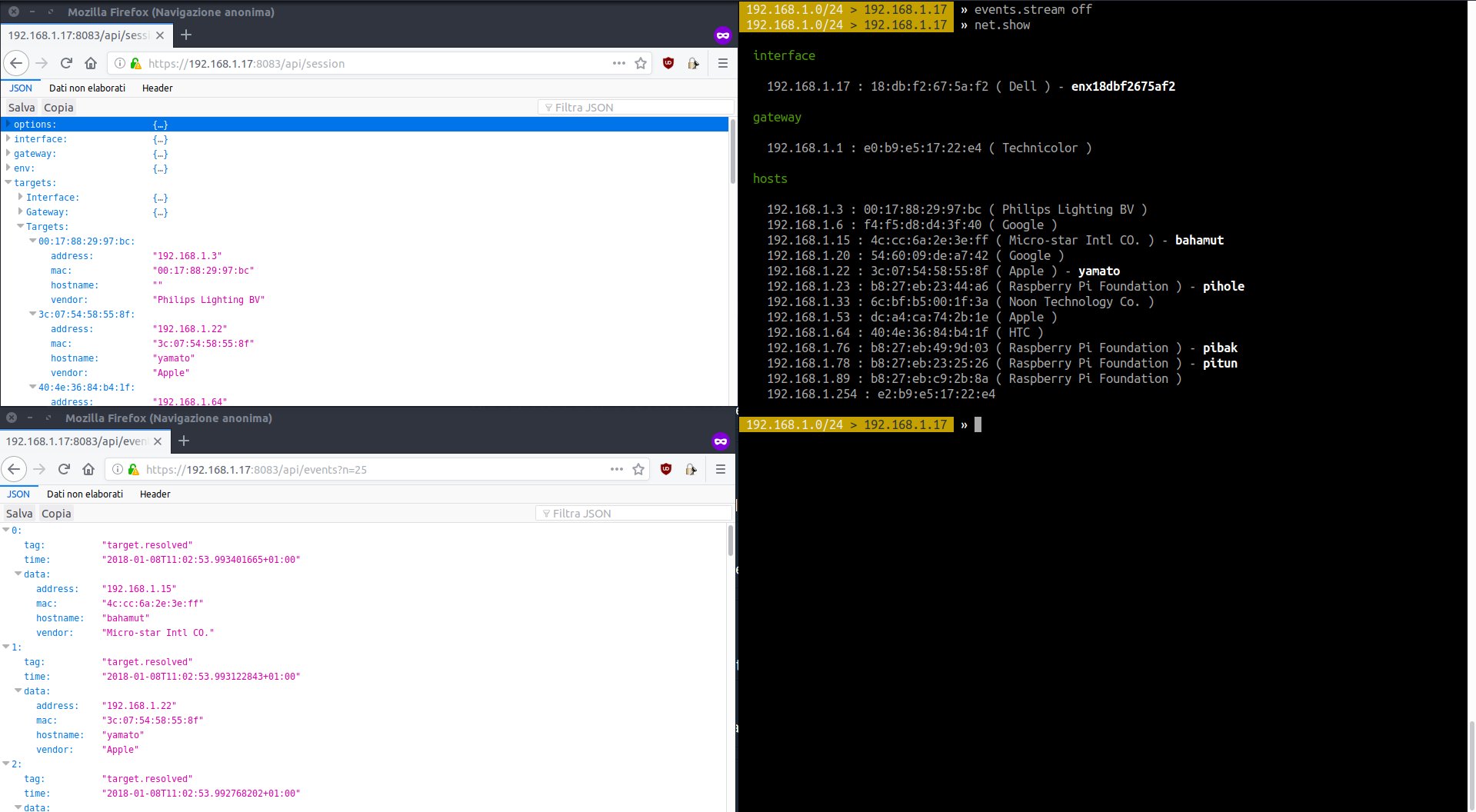
Penetration Testing with the Bash shell Penetration Testing with the Bash shell PDF eBook About This Book Utilize the command line to create, run, and execute tests Learn useful command-line based information processing utilities and unlock the problem-solving power of a Linux terminal Practical demonstrations using in-depth explanations and screenshots to help you … Read more