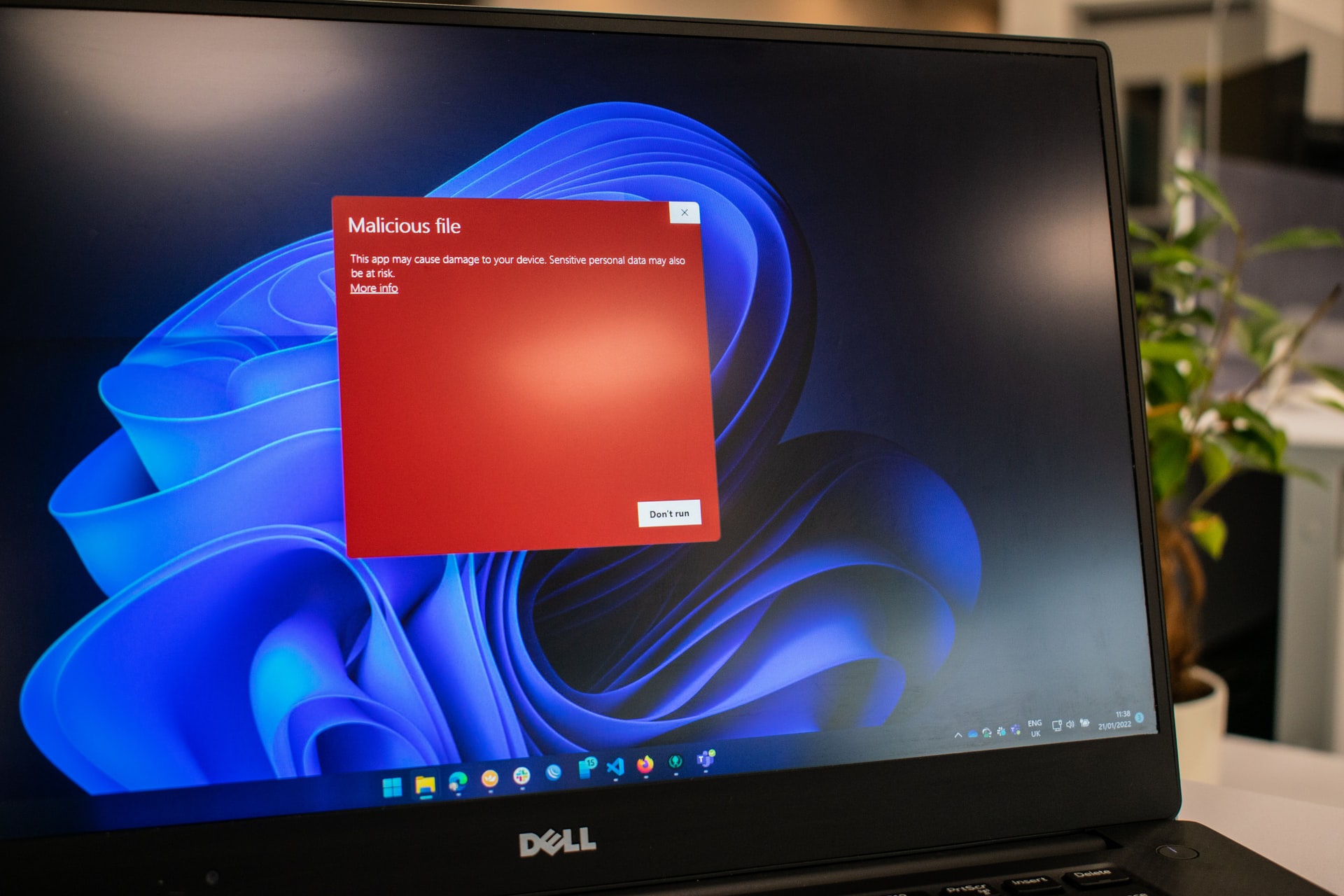
Pegasus malware was used to attack Spanish Prime Minister Pedro Sánchez’s phone
The Pegasus spying malware was used to hack the smartphones of Spain’s prime minister and minister of defense, according to the Madrid government. That’s the first verified use of the eavesdropping software against a current head of state. Last year, the phones of Prime Minister Pedro Sánchez and Defense Minister Margarita Robles were illegally hacked … Read more