mimikittenz
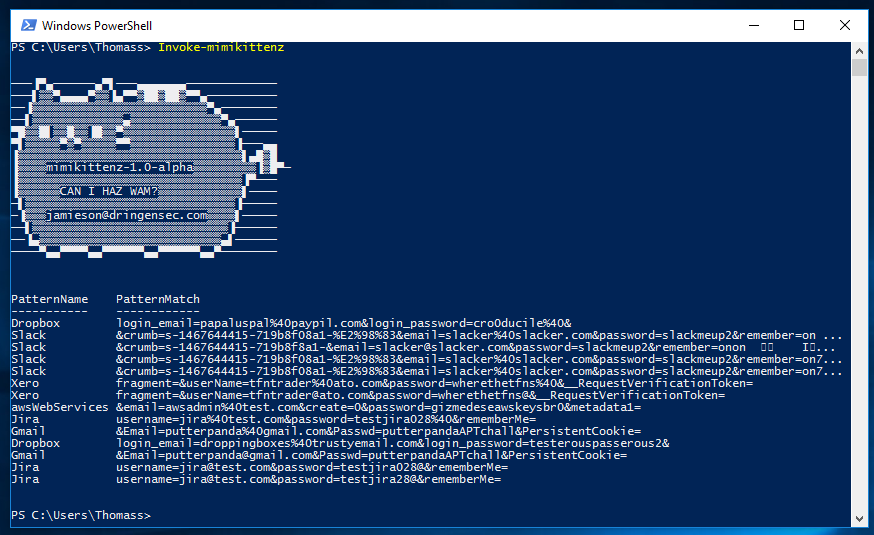
mimikittenz is a post-exploitation powershell tool that utilizes the Windows function ReadProcessMemory() in order to extract plain-text passwords from various target processes.
mimikittenz can also easily extract other kinds of juicy info from target processes using regex patterns including but not limited to:
- TRACK2 (CreditCard) data from merchant/POS processes
- PII data
- Encryption Keys & All the other goodstuff
Tool Author note: This tool is targeting running process memory address space, once a process is killed it’s memory ‘should’ be cleaned up and inaccessible however there are some edge cases in which this does not happen.
Content credits: the content listed above was provided by Putterpanda if you have a list of favorite repos nows the time to add this great tool to it credits and thanks to Putterpanda lovely tool and it works a charm. You can download Mimikittenz from the download link below please be sure to leave the author of this great tool a star on github
If you enjoyed this article please consider sharing it on social media and with your friends thanks for supporting HackingVision.
[wysija_form id=”1″]
