WordSteal – Steal NTML Hashes From Remote Computer
WordSteal This script will create a POC that will steal NTML hashes from a remote computer. Do not use this for illegal purposes. The author does not keep responsibility for any illegal action you do.
WordSteal
This script will create a POC that will steal NTML hashes from a remote computer. Do not use this for illegal purposes. The author does not keep responsibility for any illegal action you do.
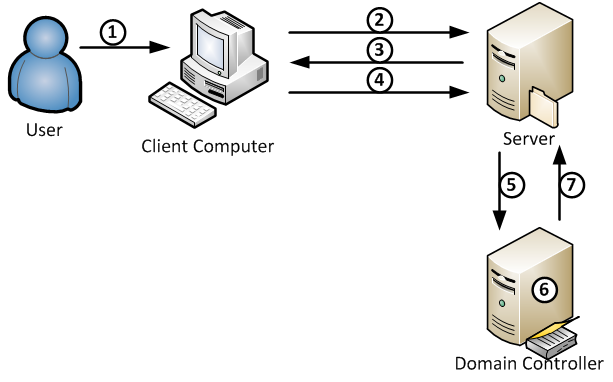
Microsoft Word has the ability to include images from remote locations. This is an undocumented feature but was found used by malware creators to include images through HTTP for statistics. We can also include remote files to an SMB server and the victim will authenticate with his logins credentials. This is very useful during a pentest because allows you to steal credentials without triggering any alerts and most of the security apps do not detect this.
Installing WordSteal (Linux)
Open up a terminal and clone WordSteal using command.
git clone https://github.com/0x09AL/WordSteal.git
Change directory to WordSteal directory.
cd WordSteal
Run WordSteal using Python.
python main.py

CREDITS: 0x09AL
DOWNLOAD WORDSTEAL
Disclaimer HackingVision.com
Any actions and or activities related to the material contained within this Website is solely your responsibility. The misuse of the information on this website can result in criminal charges brought against the persons in question. The authors of Hackingvision.com will not be held responsible in the event any criminal charges be brought against any individuals misusing the information in this website to break the law.
This site contains materials that can be potentially damaging or dangerous. If you do not fully understand please LEAVE THIS WEBSITE. Also, be sure to check laws in your province/country before accessing Hackingvision.com.
Do not abuse this material. Be responsible.
All content posted on Hackingvision.com is for educational and research purposes only. Do not attempt to violate the law with anything contained here. Administrators of this server, the authors of this material, or anyone else affiliated in any way, are not going to accept responsibility for your actions. Neither the creator nor Hackingvision.com is responsible for the comments posted on this website.