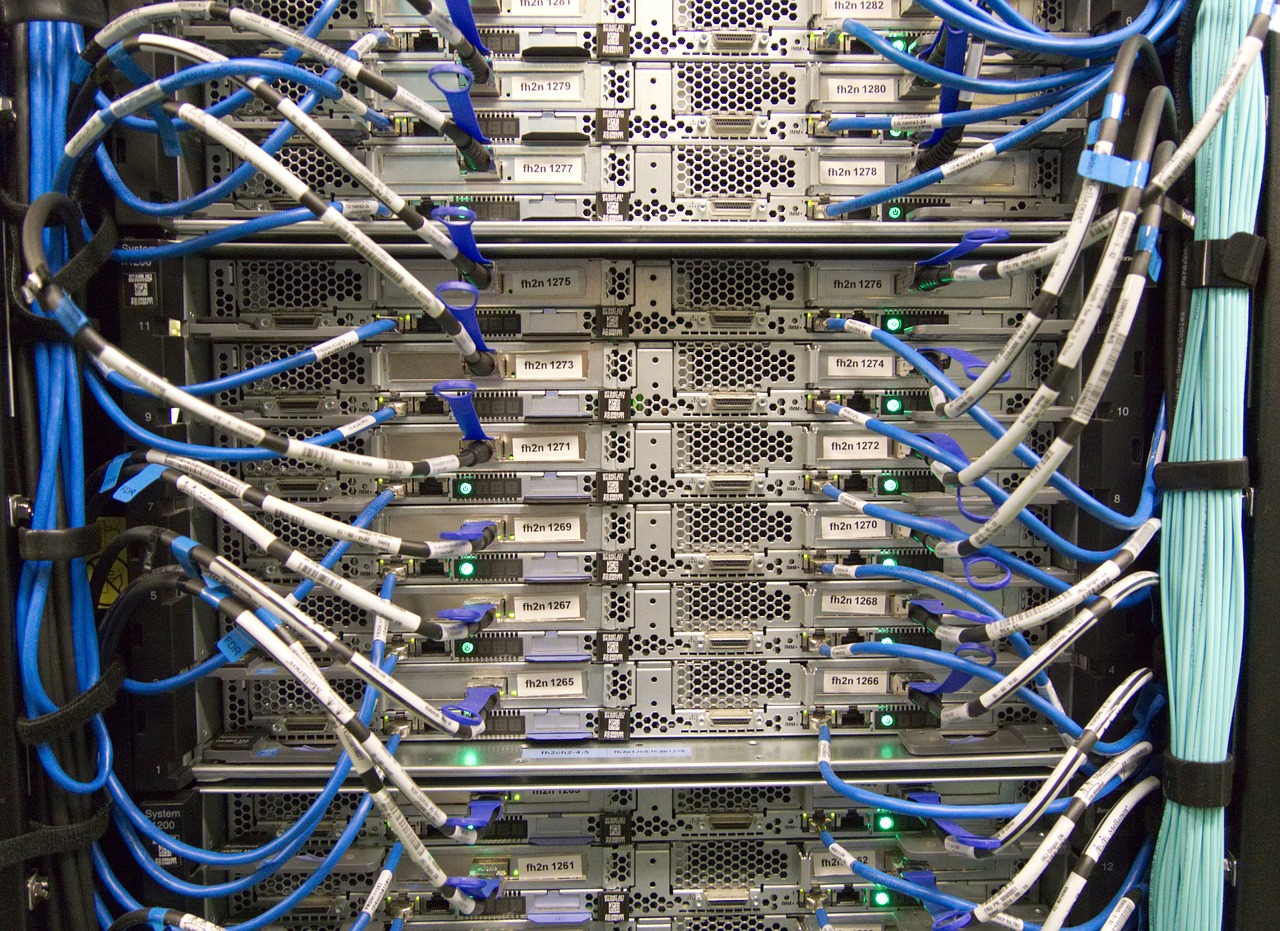
Tips on Cyber Security for Students
More than a year after the ubiquitous Covid-19 has imposed distance learning and virtualization models. Even before COVID-19 spread to online learning, most students had to use a computer every day. Whether it is chatting with classmates, writing notes, or exploring careers, technology use is essential for every student. Cyber security concerns have become an … Read more