Self Destructing Encrypted LUKs Partitions Emergency Nuke Kali Linux
Welcome back today I will show you to set up a self destructing LUKSs partition in Kali Linux this process is often referred to as an emergency nuke. Due to high demand from users the guys over at Kali.org decided to implement LUKs nuke patch into cryptsetup.
When encrypted LUKs containers or volumes are created a master key is then generated at random along with a pass-phrase to then further encrypt the master key. This allow a pass-phrase to not be directly coupled to the data or volume in question. If two sets of the same data were encrypted and the same pass-phrase was used the master keys they would remain unique to each set and could not be swapped. However this also means that if the master key was somehow lost or destroyed recovering the data would be impossible without the master key this is why is so essential to keep your master key backed up safely.
By deliberately wiping the keys this process can be categorized as a nuke. There are other ways to delete and modify your keyslots in Kali Linux but I find this one is one of the best methods.
The advantage of the Nuke patch cryptsetup option it was designed to be quick and easy, and does not require you to fully login to your Kali installation.
Scenario
Let’s assume we are traveling and we encrypt our devices using LUKs nuke patch features and the laptop or device in question gets stolen or lost this device has very important information on all the information is backed up however you are afraid of the information falling into the wrong hands to fend of thieves we could then in fact write the passphrase to our LUKs nuke setup on the system’s case. When thieves or snoops try to access the device it will allow them to boot the system however LUKs header will be destroyed any important information will be deemed inaccessible.
Let’s assume you’re being Blackmailed or threatened for the passphrase or held against your will for the passcode to the Luks container. One could then give the passphrase of the Luke nuke setup this in turn would nuke the drive and deem the information inaccessible.
Encrypting LUKs Partition With Emergency Nuke Patch Open
Open a new command terminal and use the following command to dump information of your LUKs partition.
Open a new terminal and use the following command to dump LUKs information.
root@kali-crypto:~# cryptsetup luksDump /dev/sda5 LUKS
You will see something similar to the output below the dump information shows we have slot 0 enabled with slots 1 to 7 unused we can now add our nuke key to the LUKs setup.

Now that we understand this process a little better we can now use cryptsetup to add luks nuke patch. We can now proceed and add a new nuke key to our cryptsetup.
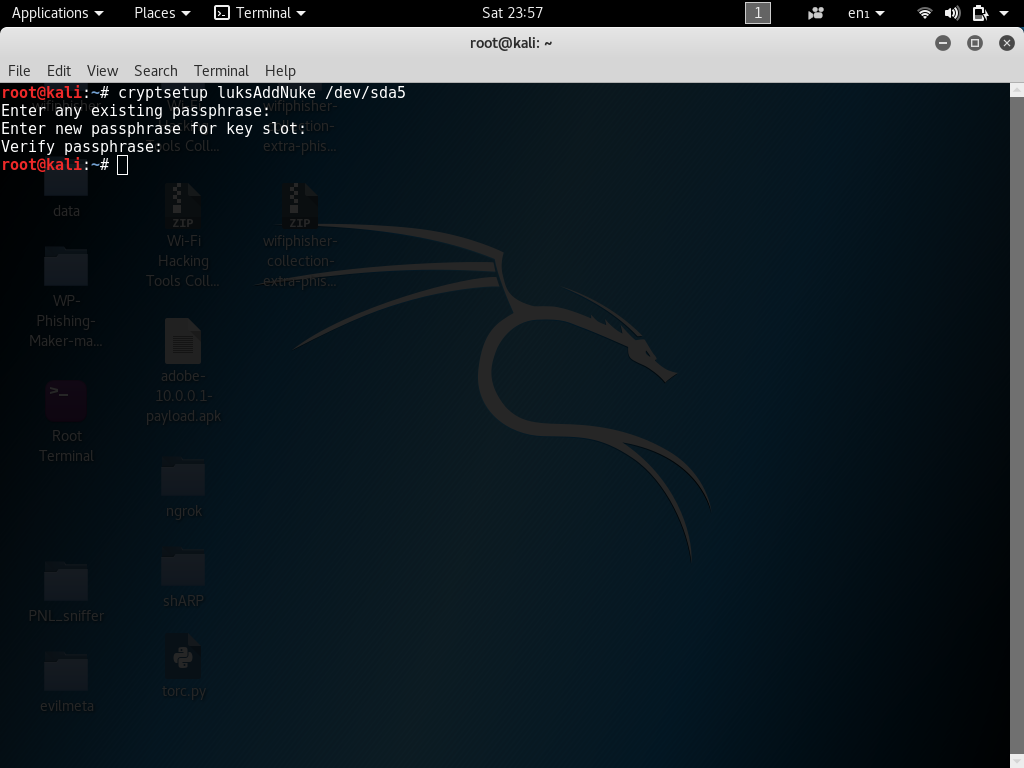
root@kali:~# cryptsetup luksAddNuke /dev/sda5
Next enter any existing passphrase: (existing passphrase) Enter new passphrase for key slot: (nuke passphrase)
root@kali: ~# cryptsetup luksDump /dev/sda5
As you can see, we have slot 0 enabled with slots 1 to 7 unused. At this point, we will add our nuke key. Backup LUKs Header Back up LUKs header file to a safe location such as an encrypted USB drive you can use whatever backup methods you like as long as the backed up header file is backed up this will allow us to restore LUKs headers files back to their original state I will explain how you can restore your LUKs header files later on in this article.

Now lets back up our LUKs Header.
root@kali-crypto:~# cryptsetup luksHeaderBackup --header-backup-file luksheader.back /dev/sda

root@kali-crypto:~# file luksheader.back luksheader.back
root@kali-crypto:~# openssl enc -aes-256-cbc -salt -in luksheader.back -out luksheader.back.enc
enter aes-256-cbc encryption password: Verifying – enter aes-256-cbc encryption password:

root@kali-crypto:~# ls -lh luksheader.back
root@kali-crypto:~# file luksheader.back

Your LUKs nuke setup is now ready.
Let’s assume we enter the pass-phrase to our LUKs nuke setup and then booted into a live USB to check out the changes to our drive as you can see below Key Slot 1 – 7: DISABLED. This means that the LUKs nuke setup worked.
root@kali:~# cryptsetup luksDump /dev/sda5
How To Restore a Nuked LUKs Cryptsetup Using LUKs Backup Header
Let’s assume it was a false alarm and you need to recover your system back to its former state to access your data we could then use a AES-256-cbc decryption password this will allow us to restore LUKs header back to its original state.
Use the commands below to restore your LUKs partition to its original state replace luksheader.back with your LUKs header your backed up earlier in the article.
root@kali:~# openssl enc -d -aes-256-cbc -in luksheader.back.enc -out luksheader.back
enter aes-256-cbc decryption password:
root@kali:~# cryptsetup luksHeaderRestore --header-backup-file luksheader.back /dev/sda5
Note: Don’t try to use your Nuke key if you have not backed the luksheader up to USB key or other storage device. To help you easily find your back up header I have set the commands above to display the output of luks back up header. Back up luks backup header to a removable USB drive for safe keeping.
Thanks for supporting HackingVision

