Finding WPS enabled AP’s Kali Linux Wash
Welcome to HackingVision, Today I will show you how to find out if a nearby router is WPS enabled in Kali Linux using Wash. A lot of modern routers support Wifi Protected Setup (WPS) and it’s quite often enabled by default by the router manufacturer or ISP.
First of all, we will need to put our wireless interface into Monitor mode this will allow us to find information about Wireless access points in range without being associated with them.
Why should I disable WPS? Exploits such as Pixie dust WPS can crack vulnerable routers with WPS turned on in seconds. Turning of WPS can help deter Wi-Fi hackers as often hackers will look for WPS enabled routers as there easy targets.
If you want to avoid attacks like this you should consider disabling WPS from your router configuration settings by going to your local IP and logging in to the admin panel of the router. Modern routers tend to lock when WPS PIN’s are being brute-forced with a tool like Reaver or Bully, This often happens after 5 or 6 incorrect PIN attempts.
Cracking WPA/WPA2 WPA Key Wireless Access Point Passphrase
Modern routers will automatically unlock after a certain amount of time some more secure routers require unlocking to be done manually in the administrator panel of the router.
Open a Terminal and use the following commands to put your wireless interface into monitor mode.
ifconfig wlan1 down iwconfig wlan1 mode monitor ifconfig wlan1 up
(Replace wlan1 with the Interface you wish to use.)

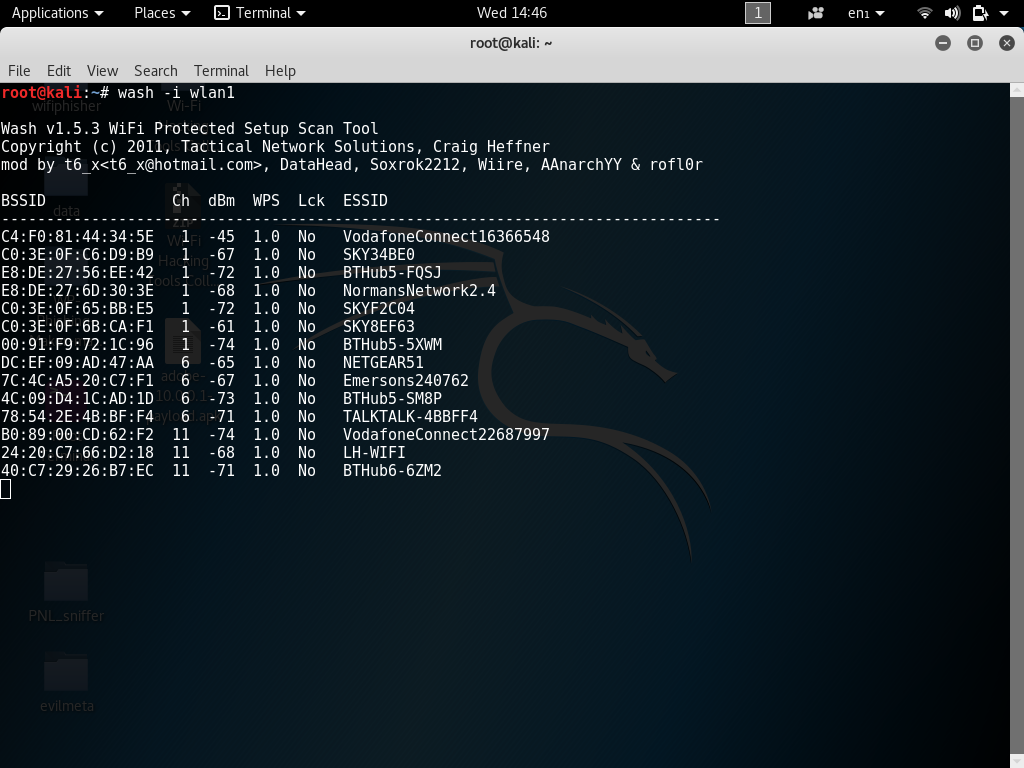
Now that our Wireless interface is successfully in Monitor mode we can now start wash and find out if Wireless Access Points in range are enabled for WPS, Wash will also tell us if the Wireless Access Point in question is locked or not this can help a lot when using various flood methods to overflow the router and reset the lock back to its default state.
To start wash in a Terminal use command.
wash -i wlan1
(Replace wlan1 with the Wireless interface you will be using.)

Rebooting WPS Locked Wireless Access Point
Modern Access Points often have better hardware and can become resistant to flooding attacks, Flood attacks are used to reset a Locked WPS router back to its default state by flooding what little resources the router has forcing it to reset.
WPS-SLAUGHTER is a Wireless testing script designed to reset locked WPS routers using multiple Wi-Fi Interfaces to see if it reboot and unlock.