Sudo Bug Allowed Linux Users To Run Commands As Superuser Root
Sudo bug found in Linux: The Linux operating system is considered a secure operating system it’s good at handling flaws and vulnerabilities, but that does not mean that it is completely safe, some bugs could still be lurking in the shadows.
The exploit is no longer relevant in the latest version of Sudo. The flaw affects all the Sudo versions prior to the latest released version 1.8.28.
One such flaw was found in Sudo function, which is widely used to run programs, scripts and execute commands with root permissions. The flaw allows any script to be executed with root privileges without the user having root access.
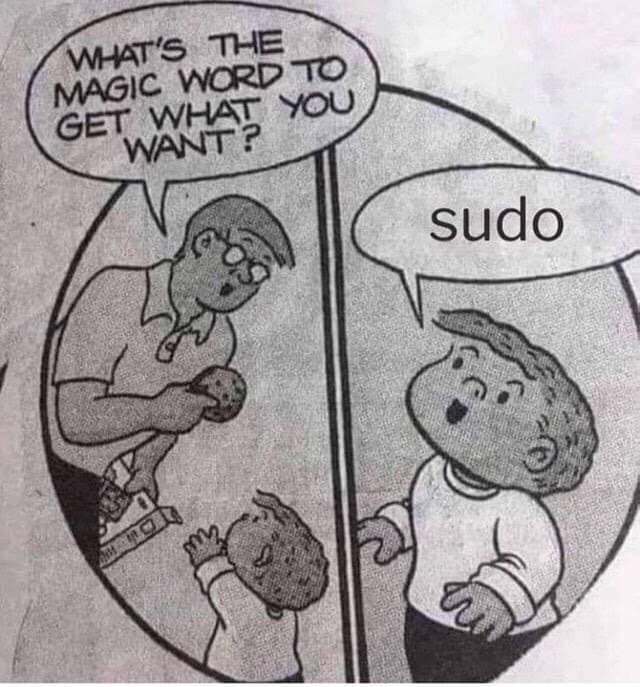
The Sudo command (superuser do) is a widely used command in the Linux operating system. Sudo is responsible for handling superuser permissions. The flaw affects all the Sudo versions prior to the latest released version 1.8.28.
The vulnerability tracked as CVE-2019-14287 and discovered by Joe Vennix of Apple Information Security. The vulnerability surprisingly could be exploited by an attacker to run commands as root just by specifying user ID “-1” or “4294967295.”
Let’s understand the design of the flaw and what exactly is causing this vulnerability.
The function which converts UID (User ID) into its username incorrectly treats -1, or its unsigned equivalent 4294967295, as 0, is always the user ID of the root user.
A word of relief is that the attack works on only specific scenarios. But all the Linux users are still recommended to upgrade to the latest Sudo version as soon as possible. Because, at the end of the day, precaution is always better than cure.
Now, for an example of an attack scenario.
If /etc/sudoers security policy configuration file says:
myhost bob = (ALL, !root) /usr/bin/vi
i.e user bob can run vi programs with any user except root.
Then the attacker can use:
sudo -u#-1 id -u OR sudo -u#4294967295 id -u
commands to execute vi with root privileges.
Check out popular YouTuber John Hammond’s video CVE-2019-14287 SUDO Bug [under 1.8.28]