Anonymous has conducted a hack of Russian state TV
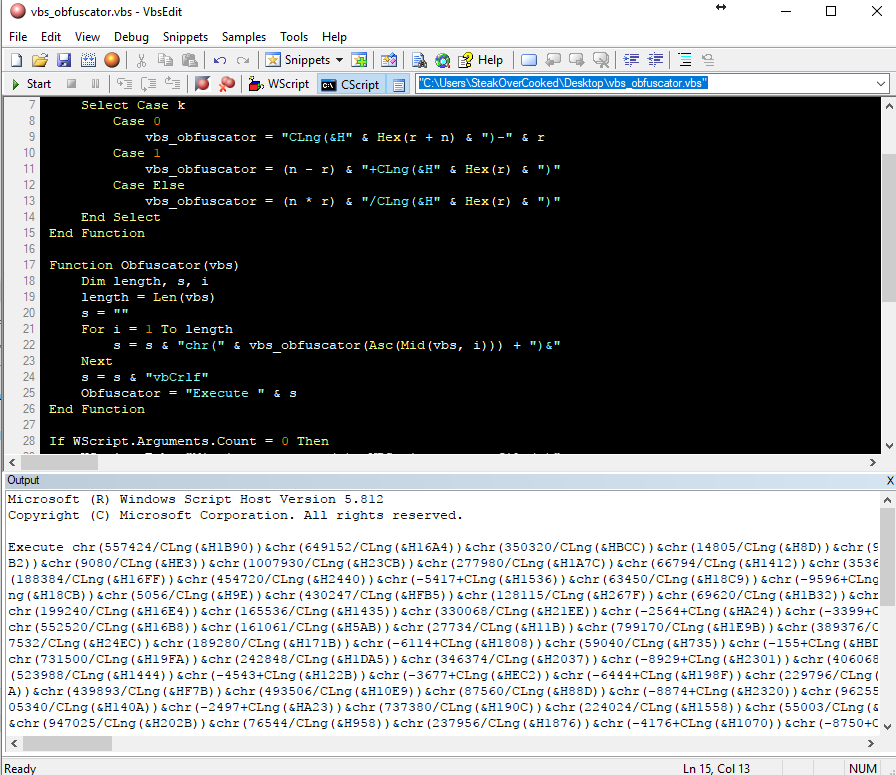
Anonymous has conducted a hack of Russian state TV in order to show the realities of the Ukrainian war. Vladimir Putin, through the use of propaganda, has been telling Russians that the invasion of Ukraine is a ‘special military operation’ and a peacekeeping exercise. Anonymous’ hacking has revealed this to be false, showing Russia’s harsh … Read more