Cloudflare’s WAF rule to protect against vBulletin RCE (CVE-2019-16759)
VBulletin RCE (CVE-2019-16759): Cloudflare is a well-known company that offers a wide range of internet services aimed at keeping your website safe. Cloudflare has recently added a new managed rule to its WAF firewall to help protect against vBulletin Remote Code Execution exploit (CVE-2019-16759).
RCE (Remote Code Execution) is an injection attack that has the ability and potential to execute extremely powerful and damaging attacks.
RCE (Remote Code Execution) attacks allow an attacker to gain privileged access to webserver or host that is possibly running vulnerable software. Elevated privileges could allow the attacker to launch malicious and damaging attacks and lead to the discovery of further vulnerabilities in the server/host system. The attacker could delete logs and other important information and destroy audit trails to hide their malicious activities. Hackers could then launch malware attacks on the host and make the host part of a zombie army Botnet that could be used to launch DDOS attacks. RCE attacks have the potential to grant a hacker access to valuable data stored in the system.
Remote Code Execution (CVE-2019-16759) in vBulletin
vBulletin 5.x through 5.5.4 allows remote command execution via the widgetConfig[code] parameter in an ajax/render/widget_php route string request.
https://nvd.nist.gov/vuln/detail/CVE-2019-16759
VBulletin (CVE-2019-16759) vulnerability is a high-severity vulnerability in vBulletin.
CVSS score: 9.8/10
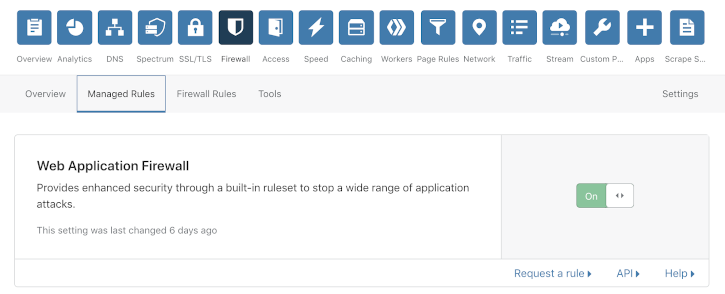
To check whether you have this protection enabled in Cloudflare, login, navigate to the Firewall tab and under the Managed Rulesets tab you will find the toggle to enable the WAF Managed Rulesets.
Next, confirm that you have the Cloudflare Specials Rulesets enabled, by checking in the Managed Rulesets card as shown below.

VBulletin Security Patch
If your using vBulletin and don’t use Cloudflare or if you don’t use Cloudflare’s managed rules you can install a patch released by vBullein.