Public WiFi Networks: Potential risks and how to work around them
Public WiFi Networks: Potential risks and how to work around them: Chances are that most people get excited when they see their device prompting to connect to public Wi-Fi when they visit a common area like a restaurant, cafe, an airport or even certain shopping malls. Many of those people tend to mindlessly connect to the Wi-Fi to get social media updates or surf the internet or watch videos on other streaming websites. What is often overlooked are the potential risks of using public Wi-Fi networks subject your device to.
Such carelessness may lead to irreversible damage to your device, its data which includes personal information, media and other sensitive information including transactional information like credit card credentials, etc.
-
Snooping in on Data
A Wi-Fi adapter usually operates on a mode called managed mode and behaves like an independent client connected to a router for internet access. This means it acts as a standalone client connecting to a single router for access to the internet. There exist certain adapters used for commercial purposes which contain a mode called the monitor mode in which the adapter captures the entire wireless traffic in a channel, with no regard to the source or recipient.
This enables the adapter to snoop in on all data from all devices including personal details and information and is a potential risk for those who connect their devices to this public Wi-Fi network. A hacker can use certain software to obtain all this information and be able to view all the URLs being visited by the users and other account details and sensitive information.

-
Fake Hotspots and clone networks
When connecting your device to public Wi-Fi, you trust the owner of the Wi-Fi. While the owner may not be interested in your personal data or any other spiteful doings, the carelessness with which he/she may set up the Wi-Fi may cause harm and pose to attract attackers. A hacker may place a fake hotspot with a similar name and may trick users into connecting to that fake hotspot and in turn steal all personal information, contacts, messages, emails and any other data that you transmit using that network.
This clone network may be present alongside the legitimate network, but users may not be able to differentiate between the two networks and hence end up as victims of a data breach. Other attackers may simply redirect your data to a duplicate fake website to steal your account and login details and credit card credentials. Hence it is important as an individual to stay aware and alert.
-
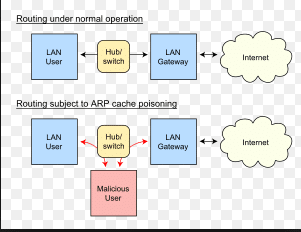
Address Resolution Protocol Spoofing
Another way to attack devices while they are connected to public Wi-Fi is by using fake ARP’s. When a device requests for the MAC address associated with a certain IP address, attackers generate fake MAC addresses with a stronger signal so that the legitimate MAC address is subdued, and the device is fooled into accepting a fraudulent address.
This can be done using a Linux software and the device data is redirected towards a fake MAC address. The fake address can also belong to a fake router which can then manipulate the traffic in the network according to his own whims and fancies.
-
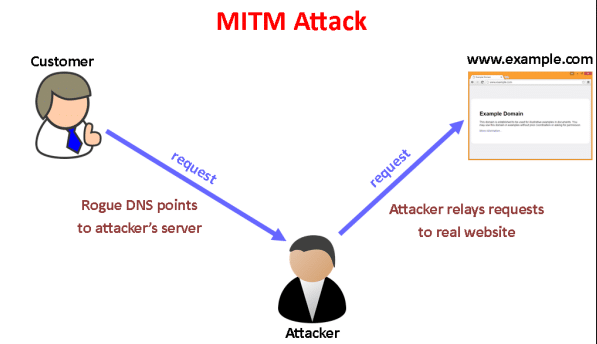
Man-in the middle attacks
In a man in the middle attack (MITM) the attacker strategically places himself in between the sender and the receiver and secretly relays messages being transferred along with the network. The attacker may simply snoop and steal information or may manipulate and alter the message on the way.
Altering the communication link between the sender and receiver helps the attacker decipher certain information like critical key values to break into encrypted texts and much more. The sender and receiver remain unaware of the fact that their network channel has been hacked.
-
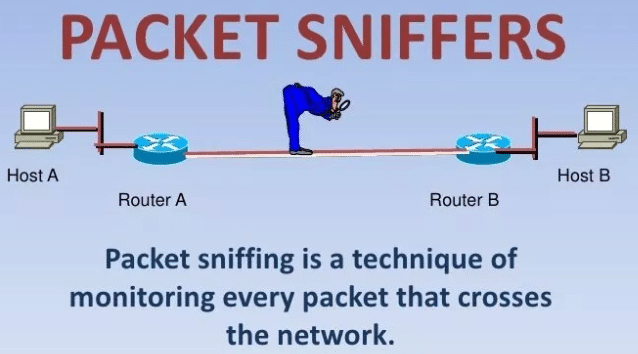
Packet Sniffing:
When you are on public WI-FI, you may encounter with packet sniffing attack. Let’s understand this attack. Packet Sniffing attack captures data packets across a network.
However, packet sniffing is used to monitor network communications and network performance. Hackers still use it to gather information while breaking into the network. The data includes passwords, protocol details, etc. that pass over the network.
While being connected to a public Wi-Fi network, your data is exposed to a variety of attacks and hence it is important to keep certain things in mind to prevent such cyber atrocities from taking place.
-
First and foremost, it is extremely important to only visit websites that are secure. Websites that are certified by SSL certificate have HTTPS as a part of their URL. Such websites make sure the data transmitted between the source and destination i.e. the server and browser are secure and safe from hackers. Top browsers prefer HTTPS while joining with public WI-FI as hackers can take advantage of insecure data transiting between the server the browser.
-
It is extremely important to have firewalls as they behave as a deterrent for potential viruses and other malicious software that may harm your device and its data.
-
Software updates should always be done regularly as these help in securing patches and vulnerabilities and hence keep your data secure.
-
Using a VPN is a key as it provided an encrypted tunnel for your data to flow so that your data remains safe regardless of the fact whether the Wi-Fi network is vulnerable or not.
Conclusion:
Hence it is essential to always keep your head on our shoulder and be proactive and prevent any damage to your device and data while connecting to public Wi-Fi. Be sure to have basic security tools in place, be wary of unprotected websites and always be alert and aware of the networks you connect with. Your data is your responsibility so b wise and try and outsmart any attempt of attacks.
If handled smartly, you can take full advantage of the services provided by the public Wi-Fi networks and at the same time keep your data safe from intruders who wish to steal and misuse your information. Be safe, be secure.
Disclaimer:
This article is a guest post, Author would like to remain anonymous for privacy reasons this article will be published by JavaRockstar.

